New Jersey’s largest hospital system said that it has paid hackers a ransom after a ransomware attack disrupted its services earlier this month.
Hackensack Meridian Health, a $6 billion non-profit health provider system based in Edison, N.J., operates 17 hospitals, nursing homes and outpatient centers, as well as psychiatric facility Carrier Clinic. The hospital system told media outlets on Friday that it was targeted by a cyberattack on Dec. 2, crippling its computer software systems for nearly five days.
“Our network’s primary clinical systems are operational, and our IT teams continue working diligently to bring all applications back online safely,” according to a statement issued to media, Friday. “Based on our investigation to date, we have no indication that any patient or team-member information has been subject to unauthorized access or disclosure.”
The attack affected the hospital’s computer software systems, from scheduling and billing systems to labs and radiology, according to reports. Consequently, the ransomware attack forced the hospitals that were part of Hackensack Meridian Health system to reschedule around 100 non-emergency appointments and surgeries earlier in December.
The hospital system did not clarify how much ransom it paid, or whether its data has since been recovered. It also did not give further indication about how systems were first infected and what data was affected. Threatpost has reached out for further comment.
“Due to developments in the investigation, and on advice of national experts, we could not disclose that this was a ransomware attack until now,” the statement said.
Ransomware Attacks Soar
The healthcare industry continues to be battered by security incidents; in October in fact, healthcare data breaches soared 44 percent month-over-month, with 661,830 healthcare records being exposed or stolen during the month.
“It’s shocking that a few years after WannaCry and NotPetya, the healthcare industry is still not prepared to deal with ransomware attacks,” Joseph Carson, chief security scientist at Thycotic, told Threatpost. “You would assume that the industry would have implemented an incident response plan and a solid backup/recovery process by now. However, we still see struggles once a system is infected as it spreads through the network, forcing IT to revert to pen and paper. We have to accept that people are going to click on stuff so we need to raise the priority of implementing the principle of least privilege, which will reduce the possibility of ransomware infecting systems and spreading throughout the network.”
Other hospitals and healthcare networks that have been hit by ransomware over the past few months, including the DCH Health System. In fact, like Hackensack Meridian Health, DCH Health System in October also opted to pay out the ransom.
That’s a move that security professionals have long condemned, warning that paying the ransom in a ransomware attack could end up causing more turmoil for victims – as well as inspire other cybercriminals to launch ransomware attacks.
However, sometimes certain factors can be important when a ransomware victim is determining the timeline and damage stemming from paying a ransom versus not paying.For instance, a healthcare organization (such as Hancock Health) that was attacked and is unable to access patient data for care, putting lives at risk, might be facing different risks when it comes to paying a ransom versus the time it takes to fully recover all systems.
“The answer is never as black and white as we’d like it to be,” Rick McElroy, head of security strategy at Carbon Black, told Threatpost in an interview. “FBI recommends that ransomware victims not pay– that’s been well established. However, it’s very difficult to unequivocally stick to that.”
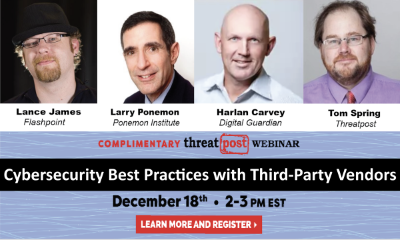
Free Threatpost Webinar: Risk around third-party vendors is real and can lead to data disasters. We rely on third-party vendors, but that doesn’t mean forfeiting security. Join us on Dec. 18th at 2 pm EST as Threatpost looks at managing third-party relationship risks with industry experts Dr. Larry Ponemon, of Ponemon Institute; Harlan Carvey, with Digital Guardian and Flashpoint’s Lance James. Click here to register.