Researchers say they have uncovered ransomware still under development that comes with a novel and nasty twist.
Infected victims of the ransomware known as Popcorn Time, have the option to either pay up, or they can opt to infect two others using a referral link. If the two new ransomware targets pay the ransom, the original target receives a free key to unlock files on their PC.
“I have never seen anything like this in ransomware. This is definitely a first,” said Lawrence Abrams who runs BleepingComputer.com and who was first to report on the Popcorn Time ransomware.
Abrams examined the code Thursday after malware forensic experts at MalwareHunterTeam tweeted they had found the code on the Dark Web. The name Popcorn Time is not to be confused with the video content app that goes by the same name.
In Abrams’ analysis of the ransomware, he said it’s unclear how far along the ransomware is from being deployed, if at all. “The code is incomplete, some of the C2 servers are not working and there are important components not yet in place.”
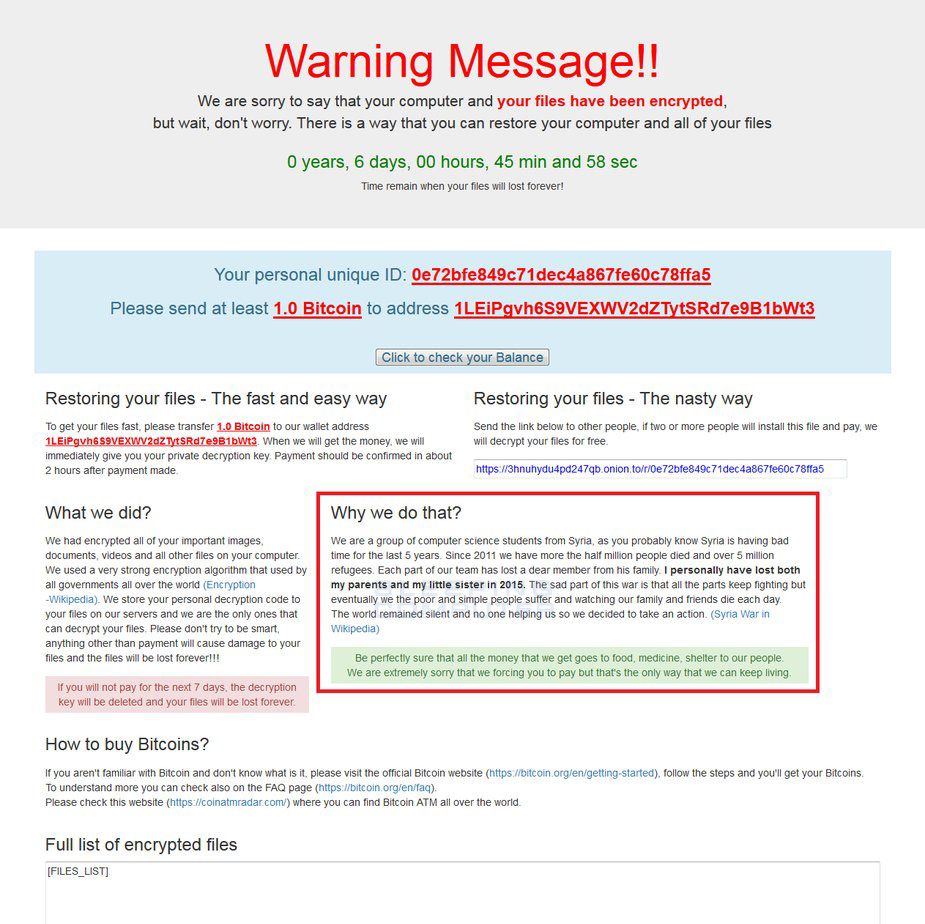
More than 500 file types are targeted by the malware, which is configured to use AES-256 encryption to lock files with the .filock extension. According to screenshots obtained by MalwareHunterTeam and BleepingComputer.com, victims are given a week to pay the ransom or find new victims. The ransom note offers two options. There is the “fast and easy way” and “the nasty way.”
“We are sorry to say that your computer and your files have been encrypted, but wait, don’t worry. There is a way you can restore your computer and all of your files… Send the link below to other people, if two or more people will install the file and pay, we will decrypt your files for free.”
According to screenshots, the ransomware developers claim to be “a group of computer science students from Syria.” The note alleges that ransomware proceeds will go to food, medicine and shelter of Syrians impacted by war. “We are extremely sorry that we are forcing you to pay,” the message reads.
The note demands 1 bitcoin (approximately $800). Victims are limited in the number of times they can input a decryption key. “There is unfinished code in the ransomware that may indicate that if a user enters the wrong decryption key four times, the ransomware will start deleting files,” Abrams wrote in a technical analysis.
The jury is still out as to how effective this strategy could be in finding new targets and making its authors money. “Will most people choose to break the law and try to infect other people? I guess not. But there is certainly a percentage of nasty people with low morals that will likely try it,” Abrams told Threatpost.