A new variant of the PowerWare ransomware is stealing street creds from the Locky strain of ransomware in an attempt to spoof the malware family. A new sample of PowerWare found by Palo Alto Networks’ Unit 42 reveals the ransomware’s quickly evolving tactics.
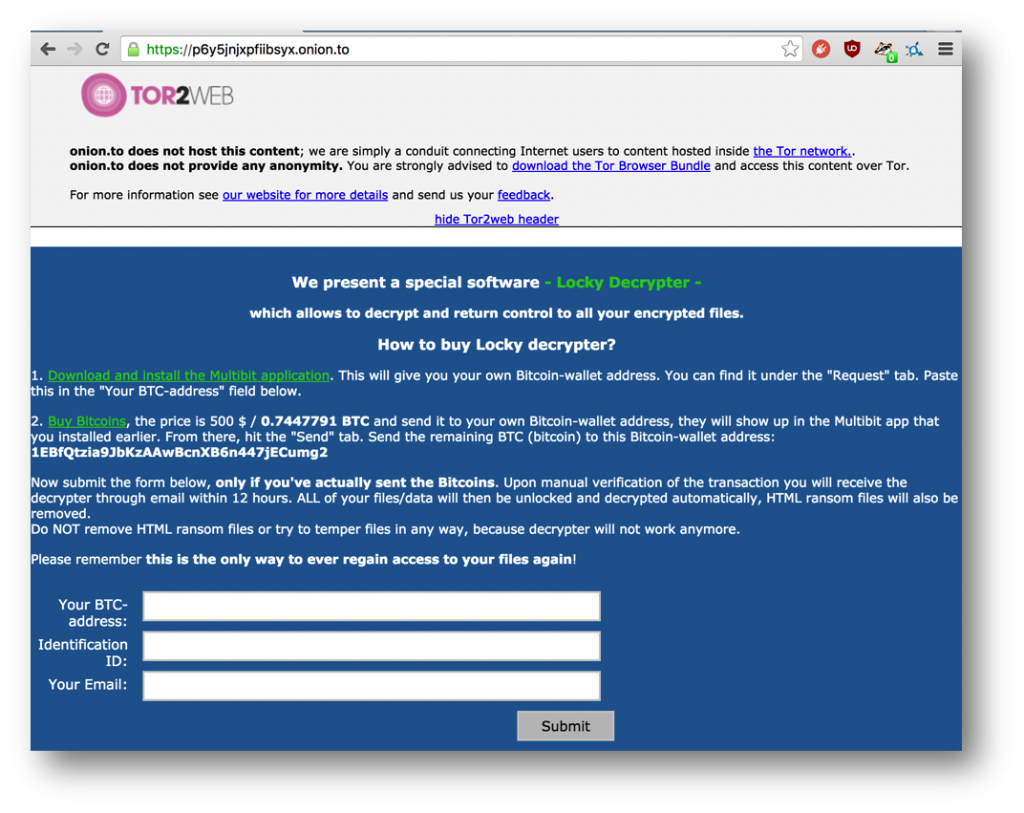
According to researchers, a new version of the ransomware is using Locky’s “.locky” file extension to encrypt files and make it appear the files have been infected with Locky. The ransomware has also adopted Locky’s ransom note and uses the same wording as Locky in the ransomware’s “help” instructions.
These attempts to mimic the far more mature and sophisticated Locky ransomware is an attempt by PowerWare authors to trick victims into thinking they are dealing with Locky, versus the immature PowerWare ransomware that can be defeated.
Compared to Locky, PowerWare uses static hard-coded encryption keys for decryption and packs a far weaker psychological punch to victims, because it is new and unknown.
“If some is infected with Locky the only way to get your files back is by paying the ransom. But PowerWare is relatively lame compared to Locky,” said Ryan Olson, intelligence director for Unit 42, Palo Alto Networks. For example, PowerWare uses AES-128 encryption and only encrypts the first 2048 bytes of the targeted files. The research team has written a Python script that can extract the static key from PowerWare ransomware and decrypt infected files.
“This is not the first time PowerWare has imitated other malware families, as earlier versions have been known to use the CryptoWall ransom note. Other instances of ransomware have also been known to borrow code from others, such as the TeslaCrypt ransomware family,” wrote co-authors of the research note, Tyler Halfpop and Jacob Soo.
PowerWare is a unique ransomware that is primarily distributed via macro-enabled Microsoft Word documents. Its hallmark is cloaking its activities by using the Windows PowerShell utility and to blend in with legitimate activity on a computer. PowerWare is a variant of the ransomware PoshCoder, which has been encrypting files since 2014.
As with PoshCoder, PowerWare victims become infected with the PowerWare ransomware if they are tricked into enabling macros on malicious Word Documents. Once enabled, the macro opens cmd.exe, which then calls PowerShell to download a malicious script. The macros are there to launch PowerShell and pull down the ransomware script. PowerWare then uses PowerShell to ultimately encrypt files stored on the machine once it’s compromised.