Smart doorbell maker Ring is giving cybersecurity critics less to gripe about with the introduction of end-to-end encryption to many of its models. Ring products, which have been a juggernaut success with consumers, have faced a litany of harsh criticism from cybersecurity experts for what they say is a lack of attention to basic digital security.
After a much anticipated response to critics, Ring this week rolled out end-to-end encryption for many of its home security camera products. End-to-end encryption, according to Ring, can be added to less than 50 percent of its in-use products. Older model smart-doorbell products, such as its first and second-generation video doorbells, cannot be upgraded with the added protection.
The move was anticipated, but initiated later than planned.

Technical specifics by the Amazon-owned company Ring were made available on Wednesday (PDF) as part of a technical preview of the new security measures. Ring’s end-to-end encryption plans was first announced in September and originally slated to be introduced by the end of 2020.
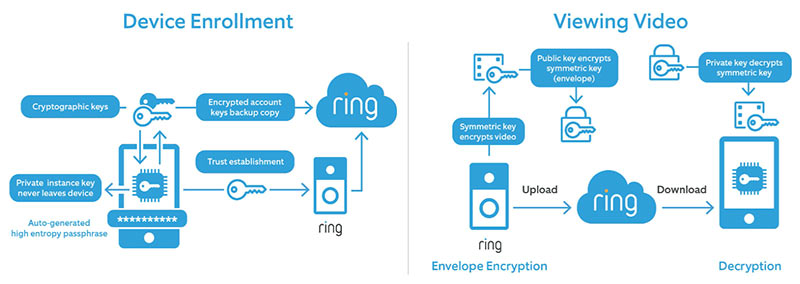
The feature—which will be optional and free for customers—will allow only the device authorized and enrolled with the associated Ring account to accept and access the live Ring video stream. If third parties want to view a recording or stream on another device, they will need access to an encryption key stored on the mobile device authorized to view the stream.
It’s unclear how law enforcements’ access to Ring doorbell feeds might be impacted – if at all.
Clamoring Critics
The company has faced years of criticism for flaws in the system that opened video and data collected by the system to be stolen by threat actors. Still other critics blasted Ring for what they said were the company’s own dodgy data-collection practices.
Last year, Amazon patched a vulnerability in the Ring smart doorbell that could have allowed attackers to access the owner’s Wi-Fi network credentials and potentially reconfigure the device to launch an attack on the home network.
A couple of days later, five U.S. Senators demanded in a letter to Amazon CEO Jeff Bezos that Amazon disclose how it’s securing Ring home-security device footage–and who is allowed to access that footage.
Last October, Ring raised privacy hackles again when it unveiled the new Always Home Cam, a smart home security camera drone that flies around homes taking security footage of people inside their own homes. Due to Amazon’s already questionable data-collection practices, privacy advocates worried that the footage could fall into the wrong hands.
Front Door Mitigations
On Wednesday, Ring outlined how it would specifically address those concerns. It said Ring will add an extra layer of security and privacy in addition to Ring’s existing encryption, which by default encrypts videos when they are uploaded to the cloud and stored on Ring’s servers, the company said.
“With End-to-End Encryption, customer videos are further secured with an additional lock, which can only be unlocked by a key that is stored on the customer’s enrolled mobile device, designed so that only the customer can decrypt and view recordings on their enrolled device,” according to a Ring blog post about the rollout.
Ring said the service gives users “control and additional choices for encrypting and decrypting their videos and is designed so that no unauthorized third party can access user video content,” according to a whitepaper Ring posted online about the service.
Videos encrypted when the feature is turned off will still be encrypted if the user decides to disable end-to-end encryption, according to the whitepaper, which also provides step-by-step instructions about how the feature works as well as specific details about what type of encryption the company is using.
End-to-end encryption certainly adds a layer of privacy that many customers and privacy advocates have long wanted from Ring, which since its inception has constantly pushed the boundaries of how much privacy people are willing to give up for home security protection.
Following Zoom’s Lead
The move to add end-to-end encryption to Ring is similar to one that online videoconferencing service Zoom took last year to encrypt video streams amid privacy concerns and numerous security breaches of the service, such as Zoom bombing and zero-day vulnerabilities, among others. Zoom, however, made the feature available to only paid users of the service.
While Ring’s new feature has privacy and security benefits, it also will disrupt some existing features of the service, such as accessing Ring video through Alexa, and Echo Show or Fire TV device, or sharing with other cameras.
The encryption also may throw a wrench in controversial plans to use Ring’s Neighbors app to share data footage from Ring devices with law enforcement, such as what’s happening in a program being tested by police in Mississippi in which they can livestream video from Ring cameras installed at private homes and businesses. When launched, the program sounded an alarm bell with privacy advocates like the Electronic Frontier Foundation, which called the launch of the program its “worst fears” being “confirmed.”
However, as the feature is optional and Ring users can choose to share encryption keys with third parties, it will still be possible to both stream video to other devices and share video streams with law enforcement if the owner of the device so chooses.
Supply-Chain Security: A 10-Point Audit Webinar: Is your company’s software supply-chain prepared for an attack? On Wed., Jan. 20 at 2p.m. ET, start identifying weaknesses in your supply-chain with actionable advice from experts – part of a limited-engagement and LIVE Threatpost webinar. CISOs, AppDev and SysAdmin are invited to ask a panel of A-list cybersecurity experts how they can avoid being caught exposed in a post-SolarWinds-hack world. Attendance is limited: Register Now and reserve a spot for this exclusive Threatpost Supply-Chain Security webinar – Jan. 20, 2 p.m. ET.