Active cyberattacks on known vulnerabilities in SAP systems could lead to full control of unsecured SAP applications, researchers are warning.
Adversaries are carrying out a range of attacks, according to an alert from SAP and security firm Onapsis issued Tuesday – including theft of sensitive data, financial fraud, disruption of mission-critical business processes and other operational disruptions, and delivery of ransomware and other malware.
SAP applications help organizations manage critical business processes – including enterprise resource planning (ERP), product lifecycle management, customer relationship management (CRM) and supply-chain management.
From mid-2020 until today, Onapsis researchers have recorded more than 300 successful exploit attempts on unprotected SAP instances.
Who’s at Risk?
Unfortunately, the ongoing attacks could have far-reaching consequences, as SAP noted in the warning:
“These are the applications that 92 percent of the Forbes Global 2000 have standardized on SAP to power their operations and fuel the global economy,” the alert noted. “With more than 400,000 organizations using SAP, 77 percent of the world’s transactional revenue touches an SAP system. These organizations include the vast majority of pharmaceutical, critical infrastructure and utility companies, food distributors, defense and many more.”
Government agencies should take particular notice of the spate of attacks, researchers said.
“SAP systems are a prominent attack vector for bad actors,” Kevin Dunne, president at Pathlock, told Threatpost. “Most federal agencies are running on SAP, as it has become the industry standard for government entities. However, these SAP implementations are often on-premise, and managed by the government entities themselves due to security concerns. These systems then become increasingly vulnerable when updates and patches are not applied in a timely fashion, leaving them wide open for interested hackers.”
The technology sector is another hot target for attacks, according to Setu Kulkarni, vice president of strategy at WhiteHat Security.
“Our reporting has found that independent software vendors (ISVs) and technology companies have and inordinately high window of exposure,” he told Threatpost. “We are seeing that ISVs and technology companies are lacking in their security rigor as they ultimately may pass on the security responsibilities to the companies that use the ISV to build products for their customers.”
Active Exploitation
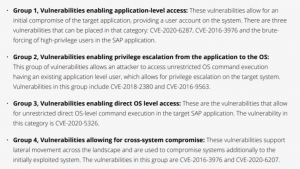
The attacks are brute-forcing high-privilege SAP user accounts, as well as exploiting a raft of known bugs: CVE-2020-6287, CVE-2020-6207, CVE-2018-2380, CVE-2016-9563, CVE-2016-3976 and CVE-2010-5326, according to the warning.
The adversaries are “advanced threat actors,” according to Onapsis, as evidenced by how quickly they’ve been able to develop exploits, among other things.
There is “conclusive evidence that cyberattackers are actively targeting and exploiting unsecured SAP applications, through a varied set of techniques, tools and procedures and clear indications of sophisticated knowledge of mission-critical applications,” the alert reads. “The window for defenders is significantly smaller than previously thought, with examples of SAP vulnerabilities being weaponized in less than 72 hours since the release of patches, and new unprotected SAP applications provisioned in cloud (IaaS) environments being discovered and compromised in less than three hours.”
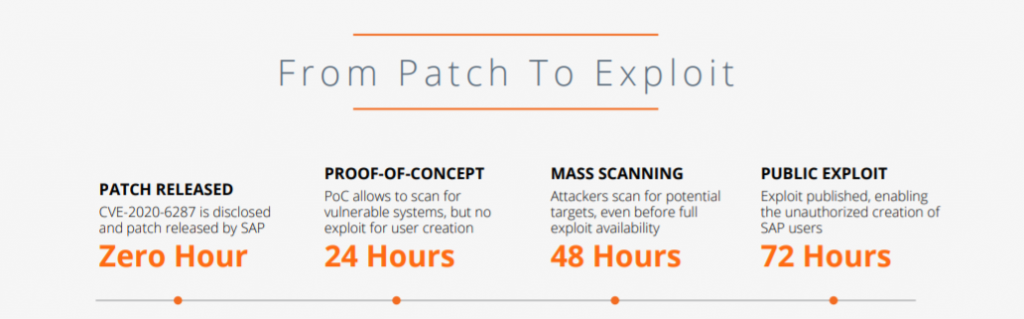
Source: Onapsis.
The issues are as follows:
- CVE-2020-6287 is a critical authentication bypass issue in SAP NetWeaver Application Server Java allowing full account takeover;
- CVE-2020-6207 is another critical authentication bypass bug, in SAP Solution Manager;
- CVE-2018-2380 is a medium-severity flaw in SAP CRM, which allows an attacker to exploit insufficient validation of path information provided by users;
- CVE-2016-9563 is also a medium-severity bug, this time in SAP NetWeaver AS Java. Remote authenticated users can exploit it to conduct XML External Entity (XXE) attacks, which allow them to interfere with XML processing;
- CVE-2016-3976 is a high-severity directory traversal vulnerability in SAP NetWeaver AS Java that allows remote attackers to read arbitrary files;
- And CVE-2010-5326 is an 11-year-old critical issue in the Invoker Servlet on SAP NetWeaver AS Java. It doesn’t require authentication, which allows remote attackers to execute arbitrary code via an HTTP or HTTPS request.
Exploit uses – click to enlarge. Source: Onapsis.
After initial access, Onapsis observed threat actors using the vulnerabilities to establish persistence, for privilege escalation, evasion and, ultimately, complete control of SAP systems, including financial, human capital management and supply-chain applications.
“Additionally, attempts at chaining vulnerabilities to achieve privilege escalation for OS-level access were observed, expanding potential impact beyond SAP systems and applications,” according to the analysis.
As an example, Onapsis said that one actor was able to scan and create an admin user utilizing an exploit utility for CVE-2020-6287. Upon successfully creating the profile and logging in, additional exploits were executed against CVE-2018-2380 for shell upload, as the attackers tried to access the operating system layer. Following that, exploits for CVE-2016-3976 were executed, targeting the download of a “credential store,” which provides access to logins for high-privileged accounts and the core database. Worryingly, this all happened within 90 minutes, according to Onapsis.
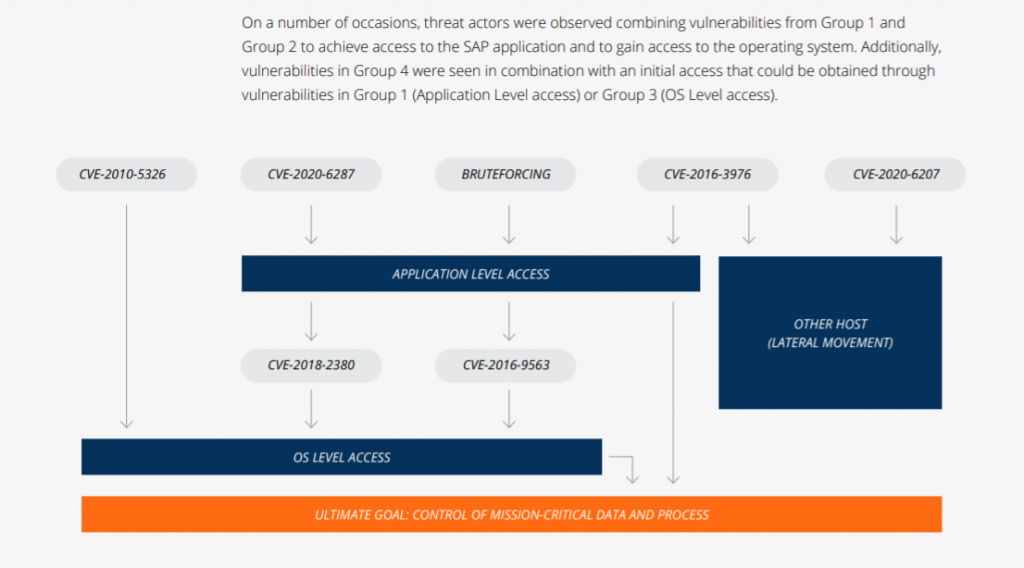
Exploit chaining. Source: Onapsis.
Interestingly, the cyberattackers in some cases are patching the exploited vulnerabilities after they’ve gained access to a victim’s environment, Onapsis said.
“This action illustrates the threat actors’ advanced domain knowledge of SAP applications, access to the manufacturer’s patches and their ability to reconfigure these systems,” according to the firm. “This technique is often used by threat actors to deploy backdoors on seemingly patched systems to maintain persistence or to evade detection.”
Who’s Behind the SAP Attacks?
The activity is being mounted by multiple groups, who appear to be engaged in coordinated activity across vast swathes of infrastructure, according to the alert.
“Attackers [are] triggering exploitation from different source systems from the ones used to perform subsequent manual logins were detected, indicating the possibility of coordinated groups and/or actors leveraging wide-spread attack infrastructure,” it reads. “While this behavior is common when analyzing operating system and network-based attacks, this data provides evidence that the same approach is also used when targeting mission-critical applications, as these actors use TOR nodes and distributed VPS infrastructures to launch the attacks and escalate privileges.”
The activity is originating from all over the world, including Hong Kong, India, Japan, the Netherlands, Singapore, South Korea, Sweden, Taiwan, United States, Vietnam and Yemen.
How Can I Prevent an Attack?
The main way to thwart these kinds of attacks is to patch the vulnerabilities. Also, any web-facing accounts should have unique passwords to disallow automated brute-force attempts to break in; and any systems that don’t need to face the public web should be taken offline.
“All observed exploited critical weaknesses have been promptly patched by SAP, and have been available to customers for months and years in some cases,” the alert noted. “Unfortunately, both SAP and Onapsis continue to observe many organizations that have still not applied the proper mitigations…allowing unprotected SAP systems to continue to operate and, in many cases, remain visible to attackers via the internet.”
Also, while applying security patches in a timely fashion is critical to closing down the risk from major, known vulnerabilities, Pathlock’s Dunne pointed out that patching can only remedy issues that are in the rear-view. With cyberattackers patching the bugs behind them, there also needs to be a way to detect malicious activity.
“For a comprehensive, forward looking approach to SAP security, organizations need to implement a comprehensive solution to monitor user activities within the system, including interactions with sensitive data,” he told Threatpost. “This way, even attackers that are able to breach SAP systems by known or unknown vulnerabilities can still be identified and their damage can be mitigated in real-time.”
Ever wonder what goes on in underground cybercrime forums? Find out on April 21 at 2 p.m. ET during a FREE Threatpost event, “Underground Markets: A Tour of the Dark Economy.” Experts will take you on a guided tour of the Dark Web, including what’s for sale, how much it costs, how hackers work together and the latest tools available for hackers. Register here for the Wed., April 21 LIVE event.











