UPDATE
Search engine optimization and analytics firm SEMrush patched a remote code execution vulnerability that allowed an attacker to send a malicious image to its service and generate a reverse shell, a typical first stage in a cyberattack. Public disclosure of the vulnerability was Monday when details of the bug were shared by a white hat hacker who boasted he had earned a bounty of $10,000 for the discovery.
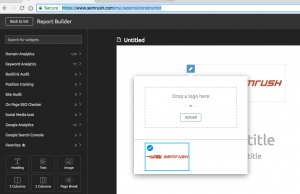
The RCE bug was tied to SEMrush’s Report Builder feature that allows users to generate custom web analytics reports using their own branding. The problem was how SEMrush handled logo images uploaded to the platform and the use of an unpatched version of ImageMagick, a web service used to process images.
SEMrush said the impact was limited to an isolated portion of its main platform. “This bug affected a specific microservice responsible for generating reports,” a company spokesperson said. “The attacker, even in the event of a successful attack on the server, under no circumstances can access the entire platform.”
According to Frans Rosén who is credited with finding the bug via the HackerOne bug bounty platform:
 “The Logo upload in the report constructor is passed through a not properly patched version of ImageMagick. You can use Postscript to get Ghostscript to run which in return allows to trigger arbitrary commands on the server, leading to Remote Code Execution.”
“The Logo upload in the report constructor is passed through a not properly patched version of ImageMagick. You can use Postscript to get Ghostscript to run which in return allows to trigger arbitrary commands on the server, leading to Remote Code Execution.”
SEMrush said the window of vulnerability was only a few days. “We would also like to mention that our platform is WAF (Web Application Firewall) secured which proactively protects our platform from attacks but a few days before report we turned it to monitoring mode to mitigate some false positive alert, that was why Frans Rosén got the opportunity to successfully exploit the issue,” the company said.
While public disclosure of the bug was Monday, SEMrush said the bug was originally reported in August of 2018 and fixed within an hour of it being reported. It said there is no evidence the vulnerability was ever exploited by a malicious actor.
 The researcher tied the ImageMagick vulnerability to a second Ghostscript flaw that could allow attackers to take remote control of systems. Ghostscript is a widely used interpreter for Adobe PostScript and PDF page description languages. Last year, Tavis Ormandy, a vulnerability researcher at Google’s Project Zero security team, discovered a Ghostscript bug and that it could allow attackers to remotely take control of a vulnerable system.
The researcher tied the ImageMagick vulnerability to a second Ghostscript flaw that could allow attackers to take remote control of systems. Ghostscript is a widely used interpreter for Adobe PostScript and PDF page description languages. Last year, Tavis Ormandy, a vulnerability researcher at Google’s Project Zero security team, discovered a Ghostscript bug and that it could allow attackers to remotely take control of a vulnerable system.
“Ghostscript contains an optional -dSAFER option, which is supposed to prevent unsafe PostScript operations. Multiple PostScript operations bypass the protections provided by -dSAFER, which can allow an attacker to execute arbitrary commands with arbitrary arguments,” wrote the U.S. Computer Emergency Readiness Team. “This vulnerability can also be exploited in applications that leverage Ghostscript, such as ImageMagick, GraphicsMagick, evince, Okular, Nautilus, and others.”
Fixes for Ghostscript were deployed in August 2018.
Researcher Rosén did not return a request for comment.
Mitigation advice from the researcher at the time to SEMrush was to “urgently make sure your policy.xml for imagemagick ONLY allows gif, jpg, png and nothing else.”
(This story was updated on 8 a.m. EDT 2/24 with a comment from SEMrush)










