Thinking about putting up smart Christmas lights but worried about your internet of things (IoT) security? You can rest a bit easier this year because at least one festive light option is a bit safer than it used to be, new research has found.
 Manufacturers of the Twinkly smart lights have taken into consideration improved security and have replaced its previously used Wi-Fi module with a more secure system-on-chip (SoC) module, according to Pen Test Partners.
Manufacturers of the Twinkly smart lights have taken into consideration improved security and have replaced its previously used Wi-Fi module with a more secure system-on-chip (SoC) module, according to Pen Test Partners.
The lights, which were born out of a 2016 Kickstarter campaign, allow users to, via smartphone, control the lights remotely, synchronize them with music, apply templates for light designs and patterns, draw and customize their own patterns, and so on.
However, there were several key security issues with the 2018 version of the lights due to the use of the ESP8266 Wi-Fi module in the lights’ control box, which researchers at the time called “a bit of a fail for IoT.”
“It has no trusted execution environment, no secure key storage, basically no significant security features at all,” researchers wrote. “Much more secure modules were available at the time, but I guess the Twinkly team chose the cheap option.”
Some security problems with using the module in the previous version of Twinkly included the fact that the waterproof control modules for outdoor lights are usually outdoors. This makes them susceptible to any passing hacker who can can open the control module, attach a couple of logic probes and could recover the Wi-Fi pre-shared key (PSK) from the system, which Pen Test Partners achieved in just a few minutes, researchers said.
Researchers also found that during the process of initial connection of the lights to a home network, an unencrypted PSK key was sent over the air that could easily be intercepted, they said.
 The good news is that researchers at Pen Test compared tests they did on the Twinkly lights (from the manufacturer LEDWORKs) last year to the new version of the lights released for the 2019 holiday season and found most of the issues to be solved.
The good news is that researchers at Pen Test compared tests they did on the Twinkly lights (from the manufacturer LEDWORKs) last year to the new version of the lights released for the 2019 holiday season and found most of the issues to be solved.
LEDWORKS replaced the ESP8266 module with the slightly more secure ESP32, which researchers mentioned in their public research about the security of the lights last year was a better option than the one already in the product.
“Now the ESP32 isn’t perfect…but it does raise the bar somewhat over the ESP8266,” researchers said in a recent blog post about the switch.
Researchers acknowledged that the manufacturer was likely more inspired to make the change because of an action by a retailer stocking the lights during the 2018 season.
Pen Test Partners had contacted the retailer last year about the security issues they found in the Twinkly lights, after which it delisted the product, demanding that the manufacturer fix the issues before it would restock the lights. At the time, LEDWORKS did not directly respond to Pen Test Partners when the researchers informed them of the issues.
The fact that the manufacturer has taken security more seriously this year is a move that could bode well as a sign that IoT device-makers are finally beginning to catch on that security starts at the device level. Commercial partners exercising their power will help that along, researchers said.
“The retailer involved has now relisted the lights, which shows that commercial pressure on manufacturers can generate results for consumers,” researchers wrote. “In future, it would be wonderful to see more manufacturers following basic security guidelines and more retailers refusing to stock products that don’t comply.”
With these problems now more or less corrected in latest version of Twinkly, people who use the lights to add sparkle to their smart home this Christmas can now feel much more secure. However, while the improvement is “progress in the right direction,” manufacturers still have a long way to go before security for most of these types of devices are robust enough for ubiquitous use in the connected home, researchers warned.
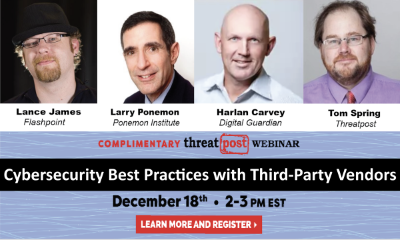
Free Threatpost Webinar: Risk around third-party vendors is real and can lead to data disasters. We rely on third-party vendors, but that doesn’t mean forfeiting security. Join us on Dec. 18th at 2 pm EST as Threatpost looks at managing third-party relationship risks with industry experts Dr. Larry Ponemon, of Ponemon Institute; Harlan Carvey, with Digital Guardian and Flashpoint’s Lance James. Click here to register.










