UPDATE: A Web site used to distribute software updates for a wide range medical equipment, including ventilators has been blocked by Google after it was found to be riddled with malware and serving up attacks. The U.S. Department of Homeland Security is looking into the compromise, Threatpost has learned.
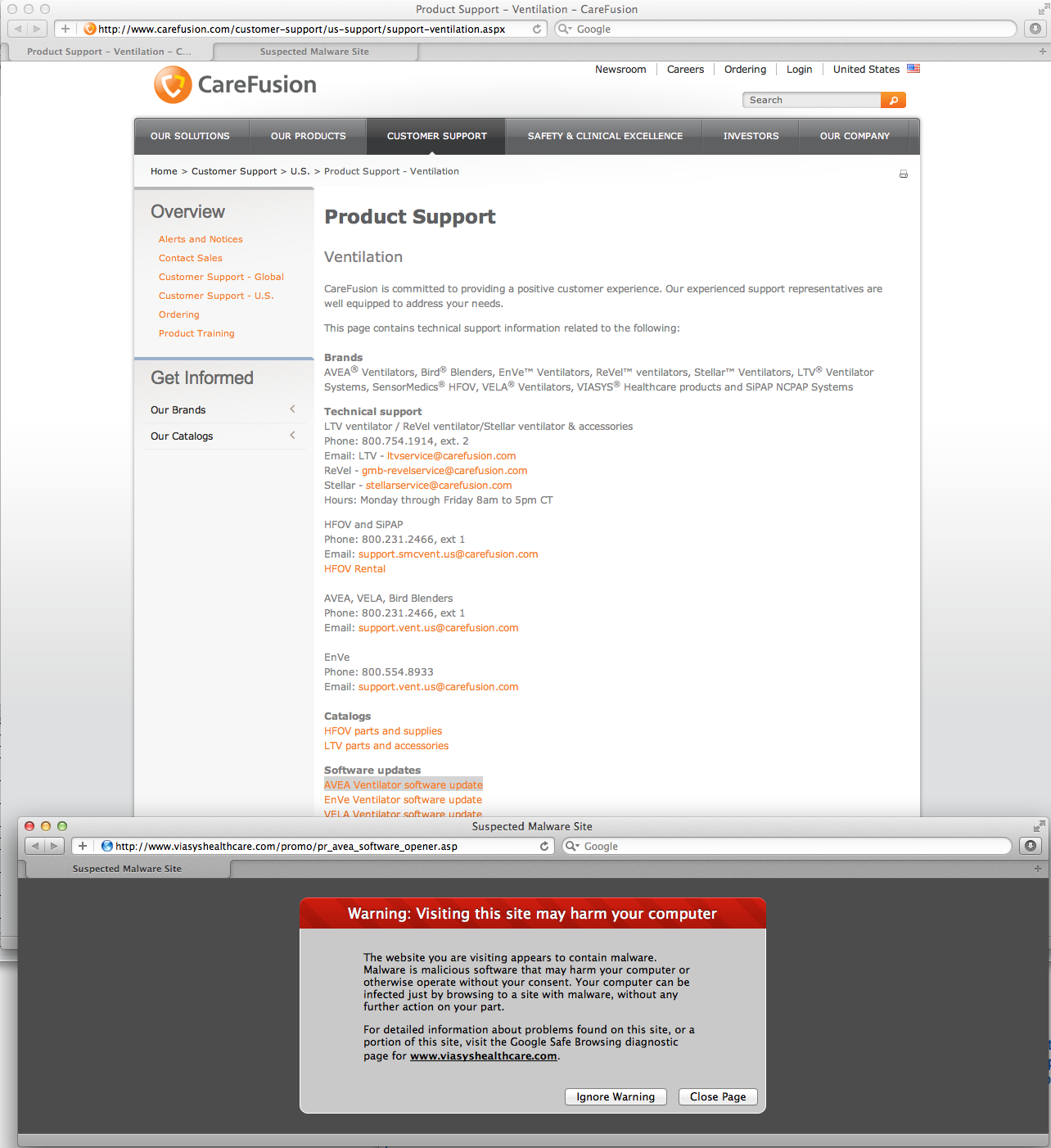
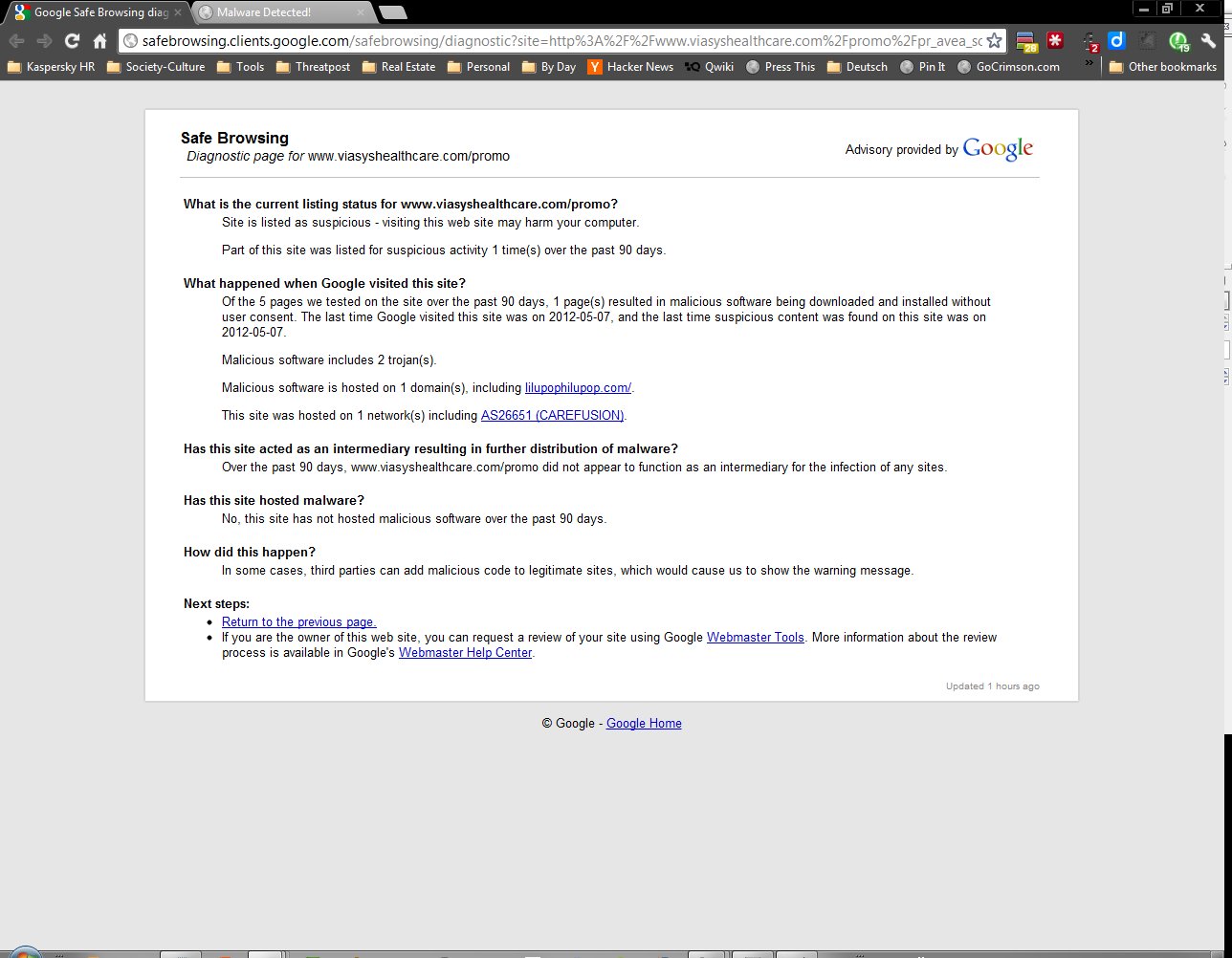
The site belongs to San Diego-based CareFusion Inc., a hospital equipment supplier. The infected Web sites, which use a number of different domains, distribute firmware updates for a range of ventilators and respiratory products. Scans by Google’s Safe Browsing program in May and June found the sites were rife with malware. For example, about six percent of the 347 Web pages hosted at Viasyshealthcare.com, a CareFusion Web site that is used to distribute software updates for the company’s AVEA brand ventilators, were found to be infected and pushing malicious software to visitors’ systems.
 The software downloaded from Viasyshealthcare.com included 48 separate Trojan horse programs and two scripting exploits, according to a review of the Google Safe Browsing report by Threatpost. Another domain, sensormedics.com, which supports CareFusion’s VELA brand ventilators, was also found to be serving “content that resulted in malicious software being downloaded and installed without user consent,” according to a June 13 scan by Google’s Safe Browsing crawler.
The software downloaded from Viasyshealthcare.com included 48 separate Trojan horse programs and two scripting exploits, according to a review of the Google Safe Browsing report by Threatpost. Another domain, sensormedics.com, which supports CareFusion’s VELA brand ventilators, was also found to be serving “content that resulted in malicious software being downloaded and installed without user consent,” according to a June 13 scan by Google’s Safe Browsing crawler.
A CareFusion did not respond to a request for comment spokeswoman said the company is “looking into the matter” and has removed the software updates from its website in the meantime.
The company makes a range of hospital equipment including the Alaris-brand infusion pumps and AVEA, AirLife and LTV series ventilation and respiratory products. CareFusion employs 14,000 people worldwide reported revenue of $2.63 billion for the first nine months of its fiscal year.
After being contacted by Threatpost on Thursday, CareFusion removed links to the infected Web sites hosting software updates for the respirators from its Product Support page. However, the company still offered links for parts and supplies for CareFusion’s 3100A High Frequency Oscillatory Ventilator (HFOV) and LTV series ventilators that were likewise infected, according to Google.
The infections first caught the attention of Kevin Fu, a professor and security researcher at the University of Massachusetts, Amherst who is a recognized expert in the security of medical devices. Fu discovered the infections when trying to download an update for the AVEA ventilators. Fu said the infections pose a major risk for hospitals that use CareFusion products.
“Vendors routinely install software updates for medical devices from the Internet or USB keys. I’ve seen medical sales engineers download pacemaker-related software from the Internet,” he wrote on his blog, Medical Device Security Center.
Fu notes that CareFusion advises customers to simply “click run” when the “file download security warning” dialog box appears – potentially tragic advice on a Web site that is serving up malicious programs such as Trojan horse programs.
Fu said an e-mail sent to an e-mail address “security@carefusion.com” bounced back. He reported the incident to the U.S. Federal Food and Drug Administration (FDA) but that the agency lacks a way to track and respond to cyber security reports for medical devices. “The reports get mixed in with general adverse event reports, and incidents with known injuries or deaths usually receive more swift attention,” Fu wrote.
Little is known about the source of the infections at CareFusion. However, an analysis by the Department of Homeland Security found that some of CareFusion’s Web sites were relying on six year old versions of ASP.NET and Microsoft Internet Information Services (IIS) version 6.0, which was released with Windows Server 2003. Both platforms are highly susceptible to compromise. DHS is continuing to investigate the incident and may refer it to its ICS-CERT division, which focuses on threats to critical infrastructure.
It is also unclear whether the attackers knew that the compromised sites hosted software for running life-saving medical devices. Attacks that leverage legitimate Web sites are common online. Recent months have brought reports of prominent Web sites and hosting firms that were hacked and reconfigured to serve up malicious programs. In April, Google warned 20,000 Webmasters about sites that may be compromised and redirecting visitors to malicious Web sites.
Fu said the warnings from Google should give CareFusion’s many customers pause before downloading updates from the company’s Web sites.
“I find it difficult to establish trust in the safety of software affiliated with reports of “malicious software being downloaded and installed without user consent.”









