A music-streaming app offered on Google Play, harboring spyware that stole victims’ contacts, files and SMS messages, made its way onto the official Android app marketplace not once, but twice.
The spyware was hidden in an app called Radio Balouch (also known as RB Music). The app itself was actually a fully-functional streaming radio app for music enthusiasts interested in listening to music from the Balouchi region – an area in eastern Iran, western Pakistan and southern Afghanistan. But behind the scenes, the app was stealing its users’ personal data.
“Besides Google Play, the malware, detected by ESET as Android/Spy.Agent.AOX, has been available on alternative app stores,” said Lukas Stefanko, security researcher with ESET in a Thursday post. “Additionally, it has been promoted on a dedicated website, via Instagram, and YouTube. We have reported the malicious nature of the campaign to the respective service providers, but received no response.”
Radio Balouch made its way past Google’s app vetting policies not once, but twice, researchers said; but was swiftly removed by Google both times after they alerted the company to it. The first app discovered was reported on July 2 and removed within 24 hours. The app then reappeared on July 13 and was again swiftly removed.
The app, which was found on Google Play at two different times and works on Android 4.2 and above, had over 100 installations each time it was found on Google Play.
Spyware Functionality
What makes the spyware stand out is that it was built on the AhMyth malware, available on Github as an open source project. This remote access tool was made publicly available in late 2017; since its release, researchers have witnessed various apps that are based on it: “however, the Radio Balouch app is the very first of them to appear on the official Android app store,” he said.
The app’s internet radio feature is bundled into the functionality of the AhMyth malware in one malicious app. While the internet radio component is fully functional and plays a stream of Balouchi music after installation, the app also has capabilities to steal contacts, harvest files stored on the device and send and steal SMS messages on the affected device.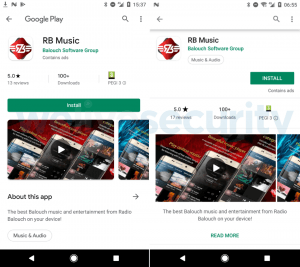
After installation, the app opens a home screen with music options, and offers the option to register and login – an option which researchers believe is actually an attempt to steal user credentials for the purposes of phishing. After installation the app also starts requesting permissions, including permission to access to files on the device (which is a legitimate permission for a radio app to enable its functionality) and to access contacts (under the guise of a functionality for the user to share the app with friends in their contact list).
Information about compromised devices and victim contact lists would be sent to a command-and-control server.
Upon further investigation, Stefanko found that the app was distributed from a dedicated website (radiobalouch[.]com), which utilized a server that was also used for the spyware’s command-and-control communications. The domain was registered on March 30, 2019, but was taken down shortly after the apps were reported.
Despite being removed from Google Play, the malicious radio app is still available on third-party app stores as of Thursday, researchers said.
Google Play
The incident throws Google Play’s app vetting processes into question. The official Android app marketplace has continued to weed out malicious apps delivering bad functions, from adware to mobile trojans.
Earlier in 2019, Google Play removed least 85 fake apps harboring adware, disguised as game, TV and remote control simulator apps. Once downloaded, the fake apps hide themselves on the victim’s device and continued to show a full-screen ad every 15 minutes. Last year, Google removed 22 malicious adware apps ranging from flashlights, call recorders to WiFi signal boosters that had been downloaded up to 7.5 million times from the Google Play marketplace. And, an Android app booby-trapped with malware was recently taken down from Google Play in November — after being available for download for almost a year.
“The (repeated) appearance of the Radio Balouch malware on the Google Play store should serve as a wake-up call to both the Google security team and Android users. Unless Google improves its safeguarding capabilities, a new clone of Radio Balouch or any other derivative of AhMyth may appear on Google Play,” said Stefanko.
Google did not immediately respond to a request for comment from Threatpost.
Interested in more on the internet of things (IoT)? Don’t miss our free Threatpost webinar, “IoT: Implementing Security in a 5G World.” Please join Threatpost senior editor Tara Seals and a panel of experts as they offer enterprises and other organizations insight about how to approach security for the next wave of IoT deployments, which will be enabled by the rollout of 5G networks worldwide. Click here to register.











