When it comes to cyberattack-related reconnaissance and lateral movement activity, the manufacturing industry exhibits higher than normal rates.
That’s according to Vectra’s 2018 Spotlight Report on Manufacturing, which crunched data from more than 4 million devices and workloads from customer cloud, data center and enterprise environments. It determined that attackers who evade perimeter security at factories and production lines can easily spy, spread and steal information, largely unhindered by the insufficient internal access controls that are in place.
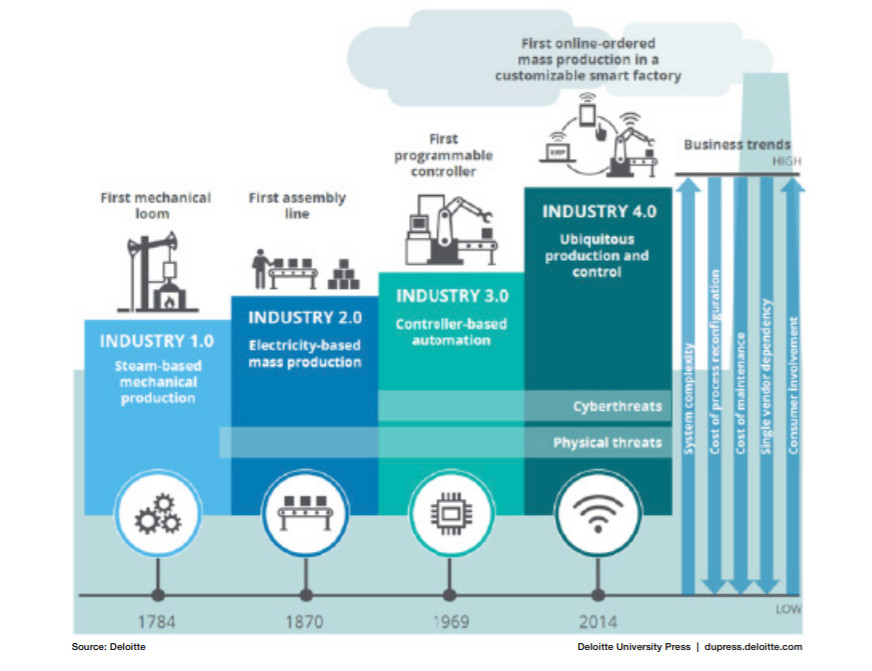
The report said that while offensives in the manufacturing space have had a lower profile compared to well-publicized attacks on retail, financial services and healthcare, the reality is that this vertical is plagued with an ever-expanding attack surface: The “Industry 4.0” trend, which is anchored in automation and data exchange in manufacturing technologies, includes the deployment of cyber-physical systems, the internet of things, cloud computing and cognitive computing.
The down side is that the rapid convergence of enterprise information technology and operational technology networks in manufacturing organizations makes the arena highly attractive to cybercriminals bent on intellectual property theft and business disruption, the report noted.
“The interconnectedness of Industry 4.0-driven operations, such as those that involve industrial control systems, along with the escalating deployment of industrial internet-of-things (IIoT) devices, has created a massive attack surface for cybercriminals to exploit,” said Chris Morales, head of security analytics at Vectra.
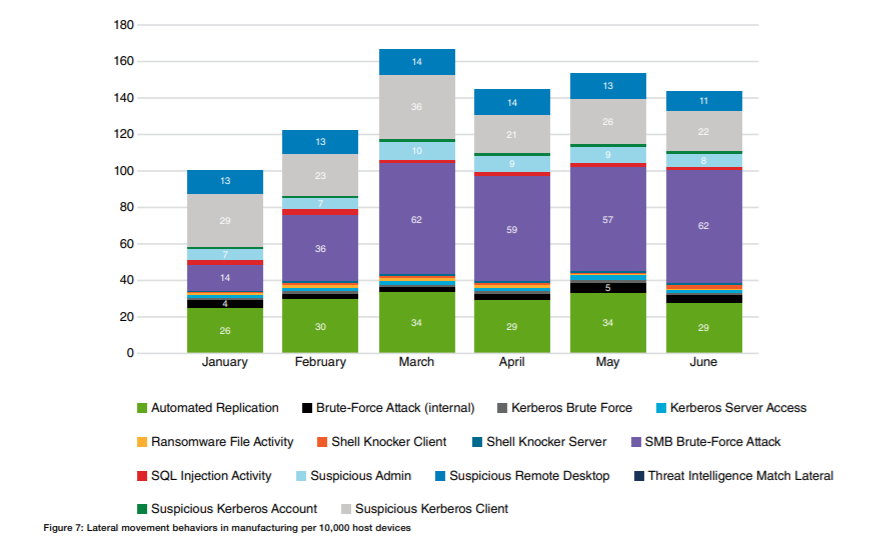
The Spotlight Report also found that manufacturing generally has a much higher volume of malicious internal behaviors than other verticals, which is a strong indicator that attackers are already inside the networks. And, an abnormally high level of lateral movement has been detected overall, which is a strong indicator that the attack is proliferating inside the network.
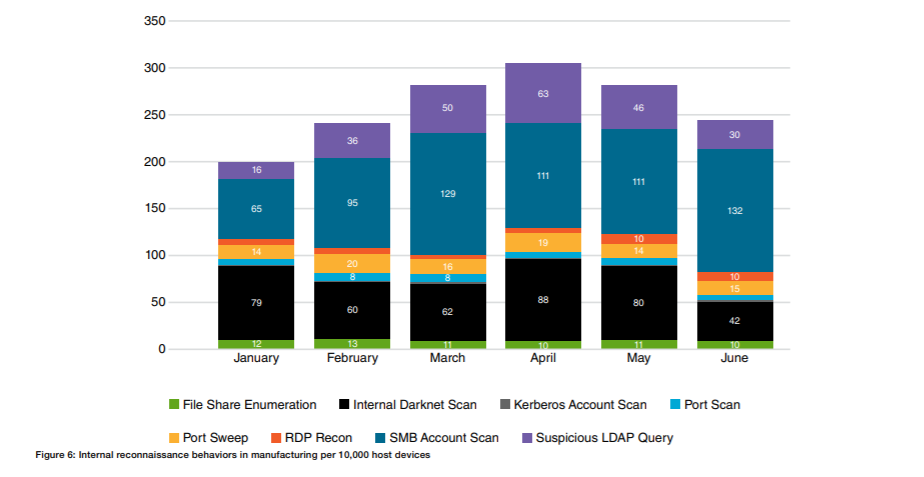
There’s also an unusually high volume of reconnaissance behaviors, which is a strong indicator that attackers are mapping out manufacturing networks in search of critical assets, Vectra noted.