A security weakness in the popular TikTok video-sharing service allows a local attacker to hijack any video content streamed to a user’s TikTok feed and swap it out with hacker-generated content.
Researchers created a proof-of-concept (PoC) hack using a technique called a man-in-the-middle (MiTM) attack against devices running the TikTok app. Video planted in user feeds appear to be legitimate content.
The flaw is that the TikTok app uses insecure HTTP for video content in an effort to improve the speed with which it can transfer data, researchers Talal Haj Bakry and Tommy Mysk asserted in a blog post Monday. However, this lack of protection also allows threat actors to easily identify and alter any HTTP traffic—including videos—flowing over the network, they said.
 “Like all social media apps with a large user base, TikTok relies on content delivery networks (CDNs) to distribute their massive data geographically,” Bakry and Mysk wrote. “TikTok’s CDN chooses to transfer videos and other media data over HTTP. …HTTP traffic can be easily tracked, and even altered by malicious actors.”
“Like all social media apps with a large user base, TikTok relies on content delivery networks (CDNs) to distribute their massive data geographically,” Bakry and Mysk wrote. “TikTok’s CDN chooses to transfer videos and other media data over HTTP. …HTTP traffic can be easily tracked, and even altered by malicious actors.”
Bakry is a senior iOS developer at NuraLogix Corp. while Mysk is a DJ and music producer.
 The vulnerability is particularly worrisome, the two assert, as social media is used to spread misinformation and shape public opinion. This, they maintain, could make the popular video-sharing app the latest platform for threat actors to engage in spreading lies and sowing division among users of TikTok.
The vulnerability is particularly worrisome, the two assert, as social media is used to spread misinformation and shape public opinion. This, they maintain, could make the popular video-sharing app the latest platform for threat actors to engage in spreading lies and sowing division among users of TikTok.
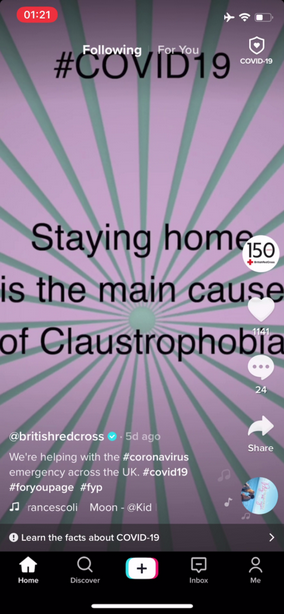
In their proof-of-concept attack, Mysk and Bakry demonstrated how popular TikTok users, using verified accounts, could have their video streams hijacked to show misleading videos downplaying the severity of the COVID-19 pandemic.
“The circulation of misleading and fake videos in a popular platform such as TikTok poses huge risks,” researchers wrote. “That encouraged us to stage a man-in-the-middle attack to swap videos and demonstrate the results.”
According to Mysk, video content, TikTok profile images and static video images are all vulnerable to attack because they are transmitted from regional content delivery networks (CDNs) using the insecure hypertext transfer protocol (HTTP) protocol instead of the encrypted hypertext transfer protocol secure (HTTPS) protocol.
Leading CDNs such as Apple and Google already have technologies and settings built into iOS and Android, respectively, that require HTTP connections to use encrypted HTTPS to secure the transmission of data. However, they both have provided a way for developers to opt-out of HTTPS for backwards-compatibility, which “should be the exception rather than the rule,” researchers wrote.
TikTok for iOS (Version 15.5.6) and TikTok for Android (Version 15.7.4) still use unencrypted HTTP to connect to the TikTok CDN, Bakry and Mysk noted. They urged TikTok, “a social networking giant with around 800 million monthly active users,” to fix the problem as soon as possible and “adhere to industry standards in terms of data privacy and protection.”
Carrying out the attack requires an adversary to control the router someone is using to access the internet and TikTok. Next, the attacker can redirect HTTP requests for video content, which is part of a TikTok user’s stream, to a hacker-controlled server. That allows the attacker to perform a MiTM attack, manipulate any data sent via HTTP and deliver hacker-controlled video content instead of the legitimate TikTok user’s content.
In their PoC, researchers hosted their forged videos on a server that mimics the behavior of TikTok CDN servers, v34[.]muscdn[.]com in a scenario that swaps out user videos for their fake ones. Because the server impersonates TikTok servers, the app cannot tell it’s an impostor, researchers said.
“The trick to direct the app to our fake server is simple; it merely includes writing a DNS record for v34[.]muscdn[.]com that maps the domain name to the IP address of our fake server,” researchers wrote. “This can be achieved by actors who have direct access to the routers that users are connected to.”
In addition to random threat actors with various agendas, others that can use the TikTok vulnerability to create and spread fake videos include: Wi-Fi operators, which can configure the router to use a corrupt DNS server; malicious VPN providers and ISPs such as telecoms which can configure a corrupt DNS server for their users; or governments and intelligence agencies, which can force ISPs to install tools that track or alter data, researchers warned.
“If you distrust any of these actors, then what you watch on TikTok may have been altered,” Bakry and Mysk wrote. “This also applies to any internet service that uses HTTP.”
Worried about your cloud security in the work-from-home era? On April 23 at 2 p.m. ET, join DivvyCloud and Threatpost for a FREE webinar, A Practical Guide to Securing the Cloud in the Face of Crisis. Get exclusive research insights and critical, advanced takeaways on how to avoid cloud disruption and chaos in the face of COVID-19 – and during all times of crisis. Please register here for this sponsored webinar.










