Trend Micro has released security updates patching five vulnerabilities in its endpoint security solutions, Apex One and OfficeScan XG for Windows.
Specifically, Apex One 2019 and OfficeScan XG SP1 and XG are affected by four critical-severity (and one high-severity) flaws. Two of these vulnerabilities are under active attack.
“Trend Micro has observed active attempts of potential attacks against … these vulnerabilities in the wild,” the company said in its Monday alert. “Customers are strongly encouraged to update to the latest versions as soon as possible.”
The first of two flaws under attack is a critical vulnerability (CVE-2020-8467) that exists in the migration tool component of Apex One and OfficeScan. The flaw could allow remote code execution on affected installations. While attackers could be remote, an attempted attack for this flaw requires authentication.
The second flaw actively targeted is a high-severity bug (CVE-2020-8468) in Apex One and OfficeScan. According to the advisory, impacted are the software’s agents that are “affected by a content validation escape vulnerability which could allow an attacker to manipulate certain agent client components. An attempted attack requires user authentication.”
Critical Flaws
The advisory also pointed to three additional critical flaws. While attempted exploits in the wild have not been observed at this time for these flaws, they all rank 10 (out of 10) on the CVSS scale, indicating the highest level of severity.
The first (CVE-2020-8470) stems from the Apex One and OfficeScan server containing a vulnerable service DLL file, which could enable an unauthenticated attacker to delete any file on the server with SYSTEM level privileges.
Another (CVE-2020-8599) exists due to the server containing a vulnerable EXE file, which could allow a remote, unauthenticated attacker to write arbitrary data to an arbitrary path on affected installations and bypass ROOT login.
And the final flaw (CVE-2020-8598) is due to the server containing a vulnerable service DLL file that could allow an unauthenticated, remote attacker to execute arbitrary code on affected installations with SYSTEM level privileges.
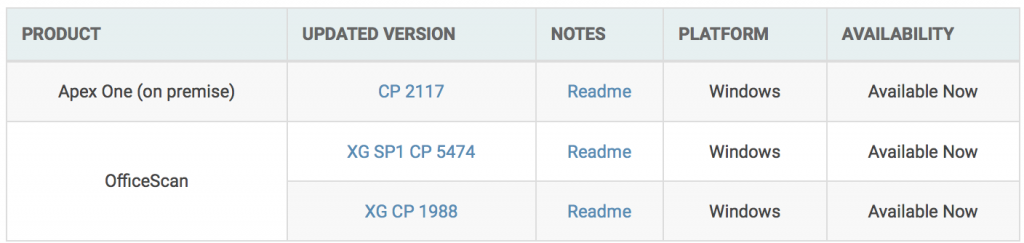
The advisory stressed that exploiting these vulnerabilities generally requires that an attacker has access (physical or remote) to a vulnerable machine. So beyond updating to the latest fixed versions (which are listed below), users “are encouraged to review and ensure the product servers and management consoles are restricted to trusted networks and/or users as appropriate.”
Trend Micro discovered all vulnerabilities in question.
Researchers with Tenable noted in an analysis posted Tuesday, this isn’t the first time attackers have singled out Trend Micro. “In October 2019, Trend Micro published a security bulletin for CVE-2019-18187, a directory traversal vulnerability in OfficeScan. According to their bulletin, they had observed active attempts to exploit the flaw in the wild,” they said. “Customers running these products should be aware that attackers will continue to exploit these vulnerabilities and search for other, undiscovered vulnerabilities in these products.”
Interested in security for the Internet of Things and how 5G will change things? Join our free Threatpost webinar, “5G, the Olympics and Next-Gen Security Challenges,” as our panel discusses what use cases to expect in 2020 (the Olympics will be a first test), why 5G security risks are different, the role of AI in defense and how enterprises can manage their risk. Register here.