A mobile spyware for Android was disclosed today, with extensive, advanced surveillance capabilities that suggest that a sophisticated actor is pulling the strings.
Using a recently discovered malware dubbed Triout, bad actors are tapping into the proliferating footprint of Android-based smartphones: The growing install base offers up a rich attack surface, filled with microphones, cameras and location-tracking capabilities that malefactors can turn into spy tools.
According to a Bitdefender analysis, the spyware’s surveillance capabilities cast a wide net, vacuuming up large amounts of user activity data and broadcasting all of it to an attacker-controlled command-and-control (C&C) server.
More specifically, a closer look at the malware showed that Triout records every single call a user makes as a media file, then ships them off to the C&C packaged with Caller ID information. It also logs every incoming SMS message and the sender, captures every picture and video the user takes, captures GPS coordinates and records all call logs (including date, time, call duration and Caller ID) – and sends it all to the Triout operators.
“We believe that this is a highly targeted attack against a limited set of people, most of who are in Israel,” Bitdefender senior e-threat analyst Bogdan Botezatu told Threatpost. “We also presume that this application targets several key victims for espionage or data collection purposes. Since the application records phone calls and exfiltrates short messages, we believe that whoever gets the information has the ability to translate and make sense of the information collected. Gathering such information in a variety of languages has no real commercial value, and a local team of attackers should be fluent in dozens of languages to obtain valuable information.”
The C&C server to which the application is sending the collected data is operational, and the campaign is ongoing, according to Bitdefender. However, the full scope of Triout’s proliferation techniques, as well as its provenance, is murky, researchers said.
“It’s interesting that Triout, which is detected by Bitdefender’s machine-learning algorithms, was first submitted from Russia, and most scans/reports came from Israel,” researchers noted in a technical analysis [PDF] of the code published Wednesday. “The sample’s first appearance seems to be May 15, 2018, when it was uploaded to VirusTotal, but it’s unclear how the tainted sample is disseminated. Third-party marketplaces or some other attacker-controlled domains are likely used to host the sample.”
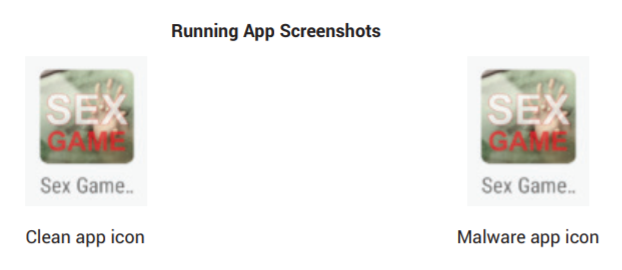
The malware was first observed lurking in an app, repackaged to look identical to a legitimate Android app called “Sex Game.” It was available in the Google Play store starting in 2016, but has since been removed.
“The malware application is almost identical to the original app, both in code and functionality, except for the malicious payload,” according to Bitdefender. “Starting from the app’s icon to the in-app screens, the malicious version seems to keep all original functionality, potentially so as not to arouse any suspicion from its victim.”
While it’s difficult to estimate the spread of the malware since the application was removed from the Play Store, Botezatu told us that the threat actors may be gearing up for a much more robust offensive.
“We presume that the attackers have now found an alternate delivery mechanism, such as the webpages they control,” he said in an interview. “Since the discovery, we were unable to isolate similar files from our malware zoo, and we initially thought that this project was abandoned. However, the command and control C&C infrastructure that collects the information exfiltrated by the malware is operational and was updated in May. This leads us to believe that the project is alive, but samples are disseminated in a controlled way to prevent them from getting into the hands of security researchers. The sample we have might have been an alpha version of the code uploaded to the store during the testing stage.”
This conclusion is bolstered by the fact that while the malware has the ability to hide itself, it doesn’t use it; in the sample that Bitdefender found, full access to the source code becomes available simply by unpacking the .apk file. This suggests the framework may be a work-in-progress or a testing phase.
“While this Trojan is extremely powerful and has the ability to record and upload phone calls, as well as use cameras and make its way into the Play Store, its code was left completely unobfuscated,” said Botezatu. “I personally think we are looking at is an alpha build of a bigger, more potent espionage tool.”