Cybercriminals hacked the official website of Tupperware, the popular food container giant, injecting a payment card skimmer into its checkout page in hopes of stealing the credit-card details of online customers.
The attackers targeted the official Tupperware[.]com website, which averages close to one million monthly visits, as well as various localized versions of the site. Researchers said they first identified the skimmer on March 20 — but there’s no indication of how long the site was compromised before that. Though Tupperware never responded to multiple attempts at contact by researchers, as of March 25, after research was publicly disclosed detailing the card skimmer, the malicious code was removed from the homepage.
“Threat actors compromised the official tupperware[.]com site…by hiding malicious code within an image file that activates a fraudulent payment form during the checkout process,” said researchers with Malwarebytes, in a Wednesday post. “This form collects customer-payment data via a digital credit card skimmer and passes it on to the cybercriminals, with Tupperware shoppers none-the-wiser.”
Researchers first came across the card skimmer during a web crawl, when they identified a suspicious iframe — responsible for displaying the payment form fields presented to online shoppers — that was loaded on the Tupperware[.]com checkout page.
Researchers said the iframe was loaded from deskofhelp[.]com, raising a few red flags. First, the webpage was newly registered (created on March 9), which is often indicative of a malicious campaign. It was also registered to elbadtoy@yandex[.]ru, an email address hosted by Russian provider Yandex – which seems strange for a payment form on a U.S.-branded website. And, it was hosted on a server at 5.2.78[.]19 (alongside a number of phishing domains).
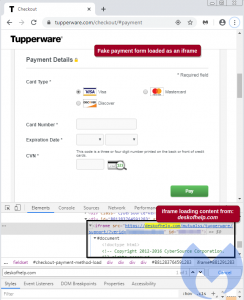 Researchers traced the rogue iframe back to code embedded in a .PNG image on the webpage. There, they found “a snippet of code on the homepage that dynamically calls an FAQ icon from Tupperware’s server, which is loaded silently (and is therefore not visible to shoppers). The image contains a malformed .PNG file that is quite suspicious.”
Researchers traced the rogue iframe back to code embedded in a .PNG image on the webpage. There, they found “a snippet of code on the homepage that dynamically calls an FAQ icon from Tupperware’s server, which is loaded silently (and is therefore not visible to shoppers). The image contains a malformed .PNG file that is quite suspicious.”
Attacker also used a unique trick to hide any traces of payment card theft. Once shoppers entered their data into the rogue iframe, they are immediately shown an “error” pretending to be a session time-out. The session time-out message is even copied from CyberSource, the legitimate payment platform used by Tupperware.
Researchers said that this enables the threat actors to reload the page with the legitimate payment form – so when victims will enter their information a second time into the (now-legitimate) form, there was no indication that the data theft had already happened. In this manner, attackers were able to steal customers’ first and last names, billing addresses, telephone numbers, as well as credit-card numbers, expiration dates and CVVs.
While the attackers were mostly careful in covering their tracks, they did make one blunder: “There is one small flaw in the integration of the credit-card skimmer: The attackers didn’t carefully consider (or perhaps didn’t care about) how the malicious form should look on localized pages,” said researchers. “For example, the Spanish version of the Tupperware site is written in Spanish, but the rogue payment form is still in English.”
Researchers say they don’t know exactly how Tupperware got hacked – but a scrape of the site showed that the company may be running an outdated version of the Magento Enterprise software, which is a popular open-source e-commerce software.
The site has now been cleaned up of remaining (client-side) artifacts. pic.twitter.com/sdOIcPAGDS
— ThreatDown (@Threat_Down) March 25, 2020
With more consumers being drawn to online shopping (due in part to many being in quarantine because of the coronavirus pandemic), web security is paramount. In the midst of this, web skimmers, which have been popular in the past with threat groups like Magecart, continue to pose a significant threat.
While Tupperware’s site has since been cleared of the skimmers, researchers said that Tupperware never responded to calls, emails and social media messages regarding the issue on their site (Threatpost has also reached out to Tupperware for further comment).
“Upon identifying this compromise, we called Tupperware on the phone several times, and also sent messages via email, Twitter and LinkedIn,” said researchers. “However, at time of publication, we still have not heard back from the company.”
Do you suffer from Password Fatigue? On Wednesday April 8 at 2 p.m. ET join Duo Security and Threatpost as we explore a passwordless future. This FREE webinar maps out a future where modern authentication standards like WebAuthn significantly reduce a dependency on passwords. We’ll also explore how teaming with Microsoft can reduced reliance on passwords. Please register here and dare to ask, “Are passwords overrated?” in this sponsored webinar.