The Department of Justice (DoJ) has charged two former Twitter employees of working with the government of Saudi Arabia to snoop on political dissidents’ accounts.
The 27-page complaint alleges that two former Twitter employees, Ali Alzabarah, 35, and Ahmad Abouammo, 41, accessed Twitter account data that helped Saudi Arabia identify the accounts’ users and their locations. In 2015, Alzabarah allegedly accessed as many as 6,000 Twitter accounts, while Abouammo accessed three Twitter accounts, both doing so without authorization. Abouammo was arrested in Seattle, Wash., on Tuesday. Alzabarah meanwhile is believed to be in Saudi Arabia; federal warrants have been issued for his arrest.
“Insider threats pose a critical threat to American businesses and our national security,” said FBI Special Agent in Charge John F. Bennett in a Wednesday statement. “The FBI will not stand by and allow foreign governments to illegally exploit private user information from U.S. companies. These individuals are charged with targeting and obtaining private data from dissidents and known critics, under the direction and control of the government of Saudi Arabia.”
Alzabarah is a Saudi citizen who resided in California and worked as a site-reliability engineer at Twitter from 2013 to 2015; Abouammo is a U.S. citizen who worked at Twitter between 2013 and 2015 as a media partnerships manager, responsible for the Middle East and North Africa (MENA) region, according to court documents.
The two allegedly worked with foreign Saudi officials to access several Twitter accounts of government dissidents – which reportedly includes the account of Saudi political activist Omar Abdulaziz, who has said he’s been repeatedly targeted. Other accounts that were accessed without authorization include an unnamed “prominent critic of the Kingdom of Saudi Arabia and the Royal Family with over 1 million Twitter followers.”
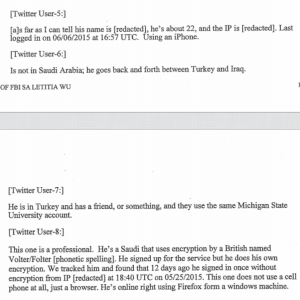
The two accessed various account information, including user emails, phone numbers, IP address information, the types of devices used, user-provided biography information, logs that contained the user’s browser info and logs of all particular user’s actions on twitter platform at any time. This information could be used to identify and locate the Twitter users who published these posts, according to the DoJ.
It’s not clear whether the two started working at the company with the alleged intent of accessing the data; or whether they were eventually convinced during their employment at Twitter. Abouammo was allegedly compensated for his illicit conduct, including with a luxury watch and $100,000 in cash.
“We would like to thank the FBI and the U.S. Department of Justice for their support with this investigation,” a Twitter spokesperson told Threatpost. “We recognize the lengths bad actors will go to try and undermine our service. Our company limits access to sensitive account information to a limited group of trained and vetted employees.”
In December 2015, court documents say Alzabarah was confronted by Twitter about his unauthorized access to accounts, and was shortly after placed on administrative leave. Alzabarah left the country the next day and submitted his resignation from Twitter by email while en route.
Also in December 2015, Twitter enhanced its controls and permissions to restrict access to user info only to those who require that access. When asked by Threatpost about what it does to prevent insider threats from accessing unauthorized data, a spokesperson said: “We understand the incredible risks faced by many who use Twitter to share their perspectives with the world and to hold those in power accountable. We have tools in place to protect their privacy and their ability to do their vital work. We’re committed to protecting those who use our service to advocate for equality, individual freedoms, and human rights.”
Insider threats continue to plague companies. This week, Trend Micro said that a rogue employee sold the data of 68,000 customers to a malicious third party, who then used that data to target customers with scam calls. Data on social media platforms, in particular, is a specific level of privacy invasion: In May, a report outlined how Snap employees were abusing their access to private user data – which includes location data, saved Snaps and phone numbers. And a report in 2018 found that Facebook had fired an employee who allegedly abused their access to data to stalk women.