A U.S. government agency was targeted with spear phishing emails harboring several malware strains – including a never-before-seen malware downloader that researchers call “Carrotball.”
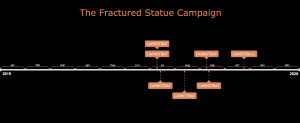
The campaign, which researchers observed occurring from July to October and code-named “Fractured Statue,” involved six unique malicious document lures being sent as attachments from four different Russian email addresses to 10 unique targets. The subject matter of the lures featured articles written in Russian pertaining to ongoing geopolitical relations issues surrounding North Korea.
“Overall, the Fractured Statue campaign provides clear evidence that the TTPs [tactics, techniques and procedures] discovered in Fractured Block are still relevant, and that the group behind the attacks still appears to be active,” said Adrian McCabe with Palo Alto Networks’ Unit 42 research group, in a Thursday analysis.
“Additionally, development and use of the new downloader, Carrotball, alongside the more commonly observed malware delivery mechanism, Carrotbat, may indicate that the previous methods employed by the group to successfully infect their targets are becoming less effective,” they said.
The Campaign
The spear-phishing emails were sent in three waves: the first, between July 15 and July 17, the second between Aug. 15 and Sept. 14, and the third on Oct. 29. The emails, which were sent from various email addresses and used varying subjects, leveraged the ongoing heightened geopolitical relations issues surrounding North Korea to lure targets into opening malicious email attachments. For instance, the subject of one of the emails was: “On the situation on the Korean Peninsula and the prospects for dialogue between the USA and the PDR.”
The emails contained files with names written in Russian and with malicious macro documents attached. The documents themselves were rather generic and had no embedded image enticements to enable macros.
Once downloaded, the malicious attachments attempted to infect victims with several malware families. The specific malware families used in the campaign consisted mainly of malicious documents featuring Carrotbat downloaders with SysCon payloads. Carrotbat, a customized dropper initially discovered on December 2017, made waves in 2018 when it was used in spear-phishing emails targeting a British government agency, which delivered lures primarily pertaining to the South Korea and North Korea region.
In that case, as in this more recent incident, Carrotbat was used to drop SysCon, a simple remote access trojan (RAT) that uses the file transfer protocol (FTP) for network communications.
Carrotball
One of the malicious documents also included a new malware downloader that researchers dubbed Carrotball. Similar to a known downloader called Carrotbat, this one’s sole purpose was to serve as the main mechanism to facilitate the download and installation of the SysCon backdoor.
“Carrotball, initially discovered in an attack during October 2019, is a simple FTP downloader utility which facilitates the installation of SysCon, a full-featured remote access trojan (RAT) which leverages FTP for command and control (C2),” said researchers. “It was found embedded in a malicious Word document sent as a phishing lure to a US government agency and two non-U.S. foreign nationals professionally affiliated with North Korea.”
Attribution
Unit 42 researchers said they assess “with moderate confidence” that the activity is related to the Konni Group. First discovered in 2014, Konni is best known for 2018 campaigns using two malware families in cyberattacks, the NOKKI malware and Carrotball.
Noteworthy is the fact that originally, the name “Konni” was used to refer to malware used in previous campaigns (with strong links to North Korean interests). However, additional campaigns began to appear with strongly overlapping TTPs but did not feature the Konni RAT, and so some researchers (including Unit 42) started using “Konni” to refer to the threat actor instead of the malware.
The use of Carrotball is one indication linking the campaign to the threat group, as the malware has previously associated with the Konni Group.
Other clues include targeting organizations who have interest in or are directly links to North Korea, and using malicious document phishing lures containing subject matter pertaining to North Korea. Researchers say that similar to this campaign, Konni Group is known for increasing the type and complexity of their payload delivery mechanisms over time.
“However, there are non-trivial obstacles to obtaining a high-confidence attribution to the Konni Group, namely the fact that previous blogs produced by Unit 42 and other researchers contain a great deal of technical detail about the group’s operations, and copycat actors may attempt to emulate previously observed TTPs to hinder attribution efforts or perform false-flag operations,” researchers warned.