MONTREAL – The Turla APT group’s extensive activities have diversified this year, representing a mix of old code, new code and fresh targets. Perhaps most interesting, this sophisticated group is branching into using scripts and open-source code in its malware development – a marked departure for an APT best-known for deploying a complex rootkit called Snake, traditionally focused on NATO-related targets.
Russian-speaking Turla (a.k.a. Snake, Venomous Bear, Waterbug and Uroboros) is known for spy campaigns targeting Western governments as well as embassies and consulates in post-Soviet states. It’s been active since at least 2014 (and possibly earlier) developing a range of custom backdoors to carry out its work. It continually evolves both in terms of malware and targets.
“Turla is highly capable, well-resourced and they go back for years,” explained Kurt Baumgartner, a researcher with Kaspersky Lab’s threat research team, speaking at Virus Bulletin 2018 in Montreal on Thursday. “Turla is so large, and they have many, many different things going on at once. And if you look at other research, it’s also clearly bigger than just our visibility into it.”
Notable developments for the group observed by Kaspersky Lab researchers in 2018 include new versions of Carbon, which is a malware that goes back to 2014; a modified version of its Mosquito malware; and a continued evolution of its IcedCoffee and KopiLuwak binaries.
As for Carbon, Baumgartner said that in 2018 it received a new orchestrator and other updates, and that it has been reliably deployed against government and foreign affairs related organizations in Central Asia all year – an attack pattern that he expects to continue into next year.
“The Carbon framework [ties] together the older, elegant and functional codebase sometimes called ‘Snake lite’ with ongoing efforts to selectively monitor high-value targets,” Kaspersky Lab researchers said in a posting on their latest Turla research, released on Thursday in tandem with the Virus Bulletin talk. “It appears that the backdoor is pushed with meterpreter now. And, as we see code modifications and deployment in 2018, we predict more development work on this matured codebase along with selective deployment to continue into 2019.”
The team also has seen a modified version of Mosquito buzzing around in recent months – now with open-source tooling being bundled into it from the Metasploit project. Turla is using Mosquito to take aim at foreign-affairs-related government targets in Europe, the Middle East, Latin America and Southeast Asia, according to the research.
“Mosquito is focused on diplomatic and governmental organizations, and it’s very consistent about that profiling,” said Baumgartner. “It’s less restrictive in its geography.”
He added that another interesting aspect of Mosquito is its delivery by man-in-the-middle (MiTM) attacks, which were seen last year: “The installers that we have seen that support the hypothesis that in all likelihood, there are WiFi based MiTM techniques are going on.”
Kaspersky Lab’s telemetry shows that download sessions with Adobe’s website were intercepted and injected to deliver Mosquito trojanized installers, which demonstrated consistent WiFi credential theft.
“Meanwhile, injection and delivery techniques are undergoing changes in 2018 with reflective loaders and code enhancements,” according to the research. “We expect to see more Mosquito activity into 2019.”
In 2018, both Turla’s Mosquito and Carbon projects focused mainly on diplomatic and foreign affairs targets, although the APT also targeted scientific and technical centers, and organizations outside of the political arena came under focus as well.
Meanwhile, a pair of related Javascript backdoors – IcedCoffee (which simply downloads other malware and is not very feature rich) and KopiLuwak (a more robust agent) – have also gained prevalence on the Turla scene.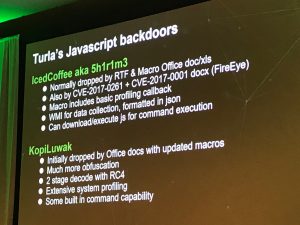
KopiLuwak was seen earlier this summer taking aim at two targets: One in the scientific and energy field, and one related to the governments in Syria and Afghanistan, showing that Turla’s KopiLuwak activity does not necessarily focus on diplomatic/foreign affairs. “Instead, 2018 activity targeted government related scientific and energy research organizations, and a government related communications organization in Afghanistan,” the researchers said. “This highly selective but wider targeting set most likely will continue into 2019.”
Kaspersky Lab researcher Mike Scott also flagged a KopiLuwak/Zebrocy code overlap. Zebrocy is a malware used by a different threat group, observed this summer.
“The third layer in the code is exactly the same between the two,” he said, speaking at Virus Bulletin. “That indicates that the same tool or generator is building these. I couldn’t find any other samples that match these, so they’re tied. Whether one group saw the code and took it, or if they’re collaborating, maybe talking about it over beers or whatnot, who knows.”
Taking the findings together, the researchers believe the Turla group is taking on a new overall shape – especially as regards the use of ready-made code.
“There is a decided shift by Turla towards increased use of open-source tools in their malware,” said Baumgartner. “This is a surprise from Turla. They used an incredibly complex root kit for years, to attack high-profile, interesting targets, and now they’re moving to scripts and open source. They haven’t been using a lot of zero-days either – in fact, there’s been none in 2018. We’ve seen no rootkits and no waterholing. So, something is changing and shifting with this group.”
Interestingly, Turla has not been a part of the Russian hacking efforts commonly attributed to APT 28/Sofacy, nor is it part of a number of other well-known activities linked to Russian-speaking groups.
Instead, “Turla [is] quietly active around the globe on other projects,” according to the research. “It is interesting that data related to these organizations [such as the DNC] has not been weaponized and found online, while this Turla activity quietly carries on.”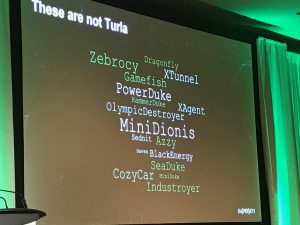
Background Turla Research
By way of background, in recent months Turla was also seen trotting out a fresh backdoor. A campaign using the new malware took aim at Germany’s Federal Foreign Office during 2017 (which the group breached after compromising the network of the country’s Federal College of Public Administration); and, Turla set its sights on the foreign offices of two European countries and a major defense contractor this year, according to IBM research from August. The 2018 efforts included new variants of the backdoor.
“The most recent versions of Turla’s invention went after targets’ inboxes by subverting Microsoft Office’s Messaging Application Programming Interface (MAPI),” IBM noted in a Tuesday posting analyzing the campaign. “They were fully controllable by email and didn’t rely on a conventional command-and-control (C&C) server. Instead, the backdoors used specially crafted PDF files in email attachments to fulfill a series of commands such as data exfiltration. The most recent variant from April 2018 was also capable of executing PowerShell commands by leveraging Empire PSInject.”
Taken together, the backdoor’s features make it hard to spot and better able to target additional marks, IBM said.
Turla’s knack for reinventing its tools and tactics is not a recent development: It was also earlier this year seen using new technique for getting code on victim machines. Researchers at ESET observed the group evolving from its previous tactic of using fake Adobe Flash Player installers to lure victims into executing malware: More recently, it has bundled a backdoor together with a legitimate Flash Player installer. And, making attacks even sneakier and harder to spot, the URLs and the IP addresses it uses appear to correspond to Adobe’s legitimate infrastructure.
“In so doing, the attackers essentially misuse the Adobe brand to trick users into downloading malware,” ESET researchers explained in a post from January on the tactic. While victims believe they’re downloading authentic software from adobe.com, the reality is that the installer tampers with the operating system’s registry to establish persistence on the system, then creates an administrative account that allows remote access.
Before that, in 2017, Turla’s Gazer backdoor was uncovered [PDF], which makes an extra effort to evade detection by changing strings within its code, randomizing markers and wiping files securely. It also employs custom encryption.
APTs in general are swift to innovate, given their profiles and goals: State-sponsored cyber-espionage for political or corporate information; complex cyber-heists on behalf of organized crime or nation-states; or efforts at spreading disinformation and wielding influence campaigns. They tend to rely on proprietary malware and are focused on making attribution difficult; they also don’t like to be detected since persistence is usually the name of the game. All of that requires staying one or more steps ahead of the defenders and security researchers – and Turla is no exception in its quest to do so.
“Turla is showing no signs of slowing down its efforts to spy on promising targets and secretly infect networks with malware for as long as possible,” IBM noted.












