Security researchers have identified a JavaScript vulnerability in the WhatsApp desktop platform that could allow cybercriminals to spread malware, phishing or ransomware campaigns through notification messages that appear completely normal to unsuspecting users. And, further investigation shows this could be parlayed into remote code-execution.
The desktop platform has more than 1.5 billion monthly active users. The high-severity bug (rated 8.2 on the CVSS severity scale) could impact those that also use WhatsApp for iPhone, if they don’t update their desktop and mobile apps, and if they don’t use newer versions of the Chrome browser.
“A vulnerability [CVE-2019-18426] in WhatsApp Desktop versions prior to 0.3.9309 when paired with WhatsApp for iPhone versions prior to 2.20.10 allows cross-site scripting (XSS) and local file reading,” according to the National Vulnerability Database. “Exploiting the vulnerability requires the victim to click a link preview from a specially crafted text message.”
More specifically, “The flaws leave users vulnerable to attacks by allowing both the text content and links in website previews to be tampered with to display false content and modified links that point to malicious destinations,” PerimeterX founder and CTO Ido Safruti wrote in a blog post, on Tuesday.
Bad actors can inject harmful code or links into “seemingly innocuous exchanges,” according to Safruti, causing unsuspecting users to click on malicious links that appear to them like messages from a friend.
“These message modifications would be completely invisible to the untrained eye,” he wrote. “Such attacks would be possible by simply modifying the JavaScript code of a single message prior to delivery to its recipient.”
However, the end game is remote code-execution — a potential outcome in some browsers, according to the researchers.
Bug Details
PerimenterX cybersecurity researcher and JavaScript expert Gal Weizman first discovered vulnerabilities leading to this latest bug in WhatsApp in 2017. He broke down the journey to discovering the latest flaw and its potential for leading to RCE in a separate post. He also said he has been working with Facebook, which owns and oversees WhatsApp, to fix the issues.
In his breakdown, Weizman showed how he started by tampering with the JavaScript for the rich preview banners of messages—the ones that include extra information regarding a link that is in the body of the message.
Through the WhatsApp desktop platform, Weizman was able to find the code where messages are formed, tamper with it and then let the app continue in its natural message-sending flow. This bypassed filters and sent the modified message through the app as usual, appearing relatively normal in the user interface. Weizman also found that website previews, displayed when users share web links, can also be tampered with before being shown.
In this way, it’s possible to inject links that redirect a user to malicious web pages or that initiate malware downloads. Further, the researcher discovered that he could also make those links look like authentic domain links — i.e., as if they really come from Facebook or other legitimate website.
“This works thanks to the role ‘@; plays in the spec of URL,” Weizman wrote. “The purpose of ‘@’ in URLs is to pass username and password to visited domains in the following way: https://USERNAME:PASSWORD@DOMAIN.COM. One can abuse this, as I just did, and replace the username and password with anything else: https://DOMAIN-A.COM@DOMAIN-B.com and it’ll still work. Firefox is the only browser that warns users, by default, In case this method is used without providing a username and password.”
It should be noted that newer versions of Google Chrome have protections against these kinds of JavaScript modifications, according to the research, while “other browsers such as Safari are still wide open to these vulnerabilities.”
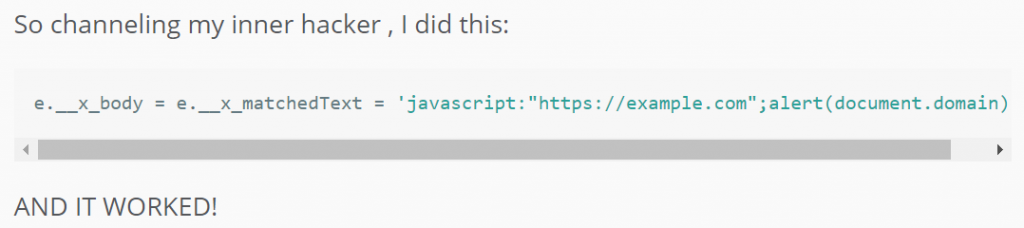
After successfully exploiting CVE-2019-18426 and performing this code injection to achieve an open redirect, the researcher took it further, to spin the hack into a persistent XSS attack through trial and error. To do so he employed JavaScript URIs (a trick that only works on non-Chromium based browsers, it should be noted):
Weizman continued probing the vulnerability to eventually bypass WhatsApp’s Content Security Policy (CSP) rules to enhance the power of the persistent XSS, which he managed to do by using Google’s CSP Evaluator. There, he discovered that the CSP lacked the object-src directive.
“Since object-src directive is missing [in the CSP], it means I can use object to load an iframe(ish) to any origin of my choice,” he wrote in the post. “That way I’ll be able to run any external code with no size limits and no problems.”
Weizman then showed how he executed malicious code on the web.whatsapp.com domain by using the XSS exploit to load the aforementioned iframe. That opens up the potential for RCE, he said.
“I then use the iframe to post a message to the top window with the content of the external code,” he explained. “The top window, where the XSS was executed, receives the message from the iframe, parses the external payload provided by it and executes it in its context (web.whatsapp.com). Win! External payload was successfully fetched and executed in the context of WhatsApp!”
The entire attack can be executed with one click from the user on the altered rich preview message.
Weizman stressed the importance of an app’s CSP rules, which could have prevented the vulnerability from being exploited in the first place.
“If the CSP rules were well configured, the power gained by this XSS would have been much smaller,” he wrote. “Being able to bypass the CSP configuration allows an attacker to steal valuable information from the victim, load external payloads easily, and much more!”
WhatsApp’s desktop platform certainly isn’t the only version of the popular messaging service to contain vulnerabilities. Last year alone, researchers found a number of flaws in the more widely used mobile app version of WhatsApp that have allowed for remote code execution, the delivery of spyware, and exposure of personal media files, among others.
Learn how Operational Technology and Information Technology systems are merging and changing security playbooks in this free Threatpost Webinar. Join us Wednesday, Feb. 19 at 2 p.m. ET when a panel of OT and IT security experts will discuss how this growing trend is shaping security approaches for IoT and 5G rollouts. This webinar is for security and DevOps engineers, IoT edge developers and security executives.