A malicious email campaign aimed at iPhone owners is making the rounds this week, using a bouquet of different themes to scam victims, just in time for Valentine’s Day – including a fake dating app.
The gambit begins far afield from romance however, with an email from “Nerve Renew,” claiming to offer a miracle cure for neuropathy. The interesting thing about this is that the email body is a picture, completely static.
“You cannot copy the contents and paste it elsewhere,” according to a Friday post from researchers at Bitdefender, who uncovered the campaign. “The sender wants to keep us inside the email body, clicking the malicious links inside.”
Those malicious links include a fake “unsubscribe” button at the bottom as well as the link behind the picture – clicking anywhere on the email body, either intentionally or inadvertently, will cause the scam to execute. Clicking the unsubscribe button takes users to a page that asks them to enter their email addresses – likely to validate whether those addresses are actually active.
Once the email body is clicked, the victim is taken on “a seemingly endless redirect loop,” until neuropathy is left far behind, and the victim lands on what purports to be a dating app for Apple’s iPhone.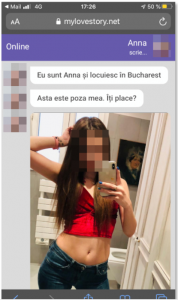
Immediately, “Anna” starts sending invitations to connect via a phone call. If the recipient takes the bait and calls, the person will be connected to a premium number and will be charged per-minute for the call.
“It’s a trap! The girl in the picture is not Anna,” the researchers said. “Rather, it’s a chatbot. And the photo was likely harvested randomly from social media.”
Interestingly, the campaign’s authors put in a little extra effort to tailor the languages of this purported “dating app” to avoid suspicion.
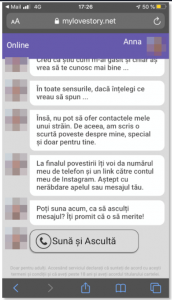 “The scammers meticulously localized their dating app to display the messages in the recipient’s language, in our case, Romanian,” the researchers explained. “Although Anna’s Romanian isn’t flawless, she could pass for a native. And she seems suspiciously interested in getting together even though she knows nothing about us.”
“The scammers meticulously localized their dating app to display the messages in the recipient’s language, in our case, Romanian,” the researchers explained. “Although Anna’s Romanian isn’t flawless, she could pass for a native. And she seems suspiciously interested in getting together even though she knows nothing about us.”
The researchers also tested the email to see if clicking on the image in the body led to the same lure each time. The second run-through took them to an entirely different scam – this one centered around a slot-machine app. In that case, the user was promised a chance to win a big jackpot and several “free spins.” Clicking on the button to spin however eventually leads to another redirect – but one that Apple’s Safari browser blocked in Bitdefender’s testing with a “Your connection is not private” message and a warning that the site could be harvesting user data.
A third click on the original email led the researchers to a sketchy VPN app, which, like Anna the chatbot, was language-localized. The swindle is a classic tech-support scam. Victims are told they’ve been infected by a virus via a security prompt that mimics the iPhone’s built-in security alerts. Clicking “OK” takes them to a website with a message that reads, “Multiple viruses have been detected on your iPhone and your battery has been infected and deteriorated. If you don’t eliminate this piece of malware now, your phone stands to incur additional damage.”
Clicking through surprisingly takes users to a legitimate app in the official Apple App Store, called ColibriVPN. Bitdefender noted that while it’s a real app, the service is shady at best.
“Upon starting, it immediately greets us with a prompt to start a free trial that gets automatically renewed after three days, and it’s easy to make expensive in-app purchases by mistake,” they wrote. “The in-app purchases are exorbitant – $61.99 for six months of full service – and the reviews are mostly fake.”
Colibri VPN did not immediately return a request for comment.
The multiplicity of the scam themes allows criminals to “preying on the diversity of people’s tastes and guilty pleasures,” the researchers said.
Users usually have several ways to spot scam emails before clicking through to the scams themselves, Bitdefender pointed out. For instance, in this case, the email sender (Nerve Renew) and the email address (lowes[at]e.lowes.com) have nothing to do with each other. The links are also shortened – a red flag.
However, mobile-first scams like this can take advantage of shortcomings in the mobile environment.
“This scam only works when you open the link on your iPhone [making it harder to inspect links],” the researchers said. “Basically, you have to long-tap the ad and use the ‘copy link’ option, then paste it elsewhere (like the Notes app) to see it. However, as we do this, iOS’s email client starts to load the link in a background preview window, essentially allowing the scam to unfold.”
These types of mobile-first scam and phishing attempts are becoming more common. For instance, also this week a banking app phishing effort was outlined by researchers, that targeted customers of more than a dozen North American banks, including Chase, Royal Bank of Canada and TD Bank. It managed to hook nearly 4,000 victims. And last year, a mobile-focused phishing kit was found that pushes links to users via email, masquerading as messages from Verizon Customer Support. These are tailored to mobile viewing: When the malicious URL is opened on a desktop, it looks sloppy and obviously not legitimate – however, when opened on a mobile device, “it looks like what you would expect from a Verizon customer support application,” according to researchers.
Learn how Operational Technology and Information Technology systems are merging and changing security playbooks in this free Threatpost Webinar. Join us Wednesday, Feb. 19 at 2 p.m. ET when a panel of OT and IT security experts will discuss how this growing trend is shaping security approaches for IoT and 5G rollouts. This webinar is for security and DevOps engineers, IoT edge developers and security executives.











