A stack of Linux backdoor malware used for espionage, compiled dynamically and customizable to specific targets, is being used as a shared resource by five different Chinese-language APT groups, according to researchers.
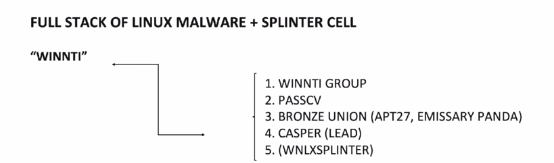
According to an analysis from BlackBerry released at Black Hat 2020 on Wednesday, those five groups have turned out to all be splinters of the Winnti Group. Active since at least 2011, Winnti is known for high-profile supply-chain attacks against the software industry, with the aim of spreading trojanized software (such as CCleaner, ASUS LiveUpdate and multiple malicious video games).
The Linux toolset uncovered by BlackBerry was used in a series of targeted attacks. It contains six different pieces, according to Kevin Livelli, director of threat intelligence at the firm. Speaking during a Wednesday session, he noted that the tools start with an installer bash script, compressed inside of another shell script, whose job it is to work with a remote build server. That build server, which is the second item in the bundle, custom-compiles a malware package for a specific target on the fly, which would then be downloaded to the victim by the installer.
This custom malware payload consists of items three and four: A rootkit and a backdoor, complete with an installation script for the target. As for the rootkit, BlackBerry researchers found two variants, both designed to work with an associated backdoor.
“We saw them tailored for different kernel versions, with up-to-date command-and-control (C2), so we knew older kernel versions were still in use – likely a reflection of the fact that many Linux sysadmins are too slow to update for various reasons,” Livelli said. “We found examples of malware that targeted Red Hat Enterprise, CentOS and Debian, but it’s a good bet, given their custom nature, and on-the-fly combination, that there are others out there.”
The fifth item is an attacker control panel, capable of managing both Windows and Linux targets simultaneously, with its own graphical user interface, Livelli said. And finally, the sixth item is the Linux XOR DDoS botnet, which is the largest known Linux botnet, first coming to notice in 2015.
As far as C2 activity, Livelli said that BlackBerry observed hard-coded network callback data inside the attacked organization it investigated, which suggests that the group had already established infrastructure inside the target before deploying the Linux stack.
“It’s highly likely that all the Linux malware that we found was not first-stage malware, but rather a persistence tool, a beachhead, if you would, and that the compromise of the targets ran much deeper and was much more well established,” Livelli said. “We also saw extensive abuse of legitimate cloud provider infrastructure [for C2].”
In addition to the C2 infrastructure and the Linux stack, it’s worth noting that other malware also infested the systems observed.
“State-backed attackers almost always target multiple platforms,” Livelli said. “This time, we found some of the same group of attackers in command of some Android malware, and others wielding some Windows malware. We found an excellent vantage point on an entire malware suite and good evidence of a cross-platform approach to espionage.”
That type of undertaking is not for the under-resourced, he added.
“The attackers took a lot of time to set this up, establish a foothold in the target, devise a way to quickly compile sophisticated malware for multiple combinations of Linux distributions and kernel versions, and then install it,” Livelli said. “That’s a lot of love, tension and development time, plus testing and refinement. And on top of that you’ve got to take care of the kids, go grocery shopping and walk the dog and you know, there’s COVID-19 social-distancing to do.”
After Livelli’s session, Kaspersky told Threatpost that the series of attacks were focused against various companies from the semi-conductor industry in Taiwan. The firm’s analysis showed that the attackers used CobaltStrike, a commercial implant, in their operations. Kaspersky also determined that the “legitimate cloud provider” mentioned that was used for C2 communications was in fact the Google Cloud platform (this makes the network traffic look legitimate and raises major issues when trying to block, according to the firm). And post-exploitation, they employed a new tool called SkeletonKeyInjector, which appears to be derived from both Mimikatz and Dumpert (two open-source projects).
Linux for Stealth
Further investigation also showed that the Linux malware set has likely been in the wild for nearly a decade. One reason for its longevity, Livelli said, is because Linux tends to fly under the radar when it comes to those holding the cyber-defense purse strings in any organization.
“Think for a minute about the people who sign the paychecks or make the big decisions,” he said. “How often does the word ‘Linux’ enter their conversations. Second, for those of us who’ve had the opportunity to work for vendors, how [deep] are the offerings for Linux compared to the offerings for Mac and Windows. I’m willing to wager that in general, security industry support of the myriad Linux distro and kernel combinations out there pales in comparison to the support given to Windows. It’s just economics, you supply the engineering and marketing and sales effort behind the platform that creates the most demand.”
As a consequence of that reality, Linux malware can slip through the cracks – while giving cybercriminals deep access to sensitive information.
“Our conclusion was that the targeting of these Linux servers was strategic in nature,” Livelli said. “I don’t have to tell anybody in this audience why the always-on, always-available nature of Linux makes it a great beachhead. How often do you take your web server or your database server offline? Is it somewhere in the neighborhood of never?”
He added that Linux-run servers constitute a deep bench of critical infrastructure within the government agencies and businesses that make up modern society.
“Linux runs not just web servers and database servers, but also proxy servers, file servers, VPN servers, stock exchange servers, it’s embedded in IoT, it’s embedded in network appliances, it’s embedded in cars,” he said. “And I don’t have to point out to this audience that Linux-run web servers are perfect for hiding massive amounts of exfiltrated data.”
Hence, APT interest in Linux is not a completely unknown quantity. According to Livelli, “Linux malware in the hands of government-backed groups has been written about before – Kaspersky Lab has documented its use by the Russian Turla and American Equation Group, and among the Chinese groups we’ve seen Linux malware research on Deep Panda and APT41…[including by] our colleagues at Chronicle. The point here is that we should be watching for this kind of thing.”
All Trails Lead to Winnti
The five individual groups found using the Linux stack were linked to Winnti and to each other in some way, Livelli noted.
For instance, “we followed a C2 trail for [one of the groups] and found some domain crossover, which led to our sample, a file that had the string called ‘wavedancer,'” he explained. “And as we took it apart, parsing some XML strings coughed up some other C2 information, which led to dual domains, which led to a domain that was registered by the same email address as had been used in lots of other PassCV work we’ve been following.”
Also, each of the groups employed a familiar Winnti technique. “Students of Winnti know that one of their hallmarks is the use of code-signing certificates, stolen from video-game companies and [more recently] certs taken from adware companies,” the researcher said.”[This] is probably the easiest common denominator to identify across these groups.”
Livelli believes that “Winnti” as a handle is actually an umbrella term that may describe shared resources rather than act as a moniker for any single APT crew. He said that he believes it’s probably a group of civilian contractors whose assembled tools are shared and that the targets are split up. Alternatively, it could be that the Chinese government is offering various groups levels of tools and support—an arrangement that FireEye called a “digital quartermaster” model.
“Whether these groups are actively collaborating, casually sharing, if they comprise some of the same members, or in actuality are smaller parts of some larger group, it’s beyond our means of analysis,” Livelli said. “But one thing is clear: This isn’t a single crew, with a one trick pony. We are looking at a long-standing, well-thought-out, richly resourced intelligence collection operation, with a sizable software engineering team to build and maintain all these tools.”
Please follow all of Threatpost’s Black Hat 2020 coverage by clicking here.
Complimentary Threatpost Webinar: Want to learn more about Confidential Computing and how it can supercharge your cloud security? This webinar “Cloud Security Audit: A Confidential Computing Roundtable” brings top cloud-security experts from Microsoft and Fortanix together to explore how Confidential Computing is a game changer for securing dynamic cloud data and preventing IP exposure. Join us Wednesday Aug. 12 at 2pm ET for this FREE live webinar with Dr. David Thaler, software architect, Microsoft and Dr Richard Searle, security architect, Fortanix – both with the Confidential Computing Consortium. Register Now.











