Voting machine-maker Election Systems & Software (ES&S) has formally announced a vulnerability disclosure policy, Wednesday, during a Black Hat USA 2020 session.
The move, which comes with the U.S. presidential elections looming in November, shows that voting-machine vendors are beginning to take the role of the security research community seriously in helping to secure critical election infrastructure. On Wednesday, ES&S said that its formally released policy applies to all digital assets owned and operated by ES&S – including corporate IT networks and public-facing websites.
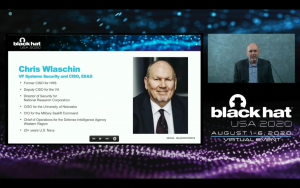
“We’re publishing this policy today to formalize how we’re going to work with security researchers to improve election security going forward,” said Chris Wlaschin, vice president of Systems Security and CISO, ES&S. “This is a good first step in the right direction and we look forward to improving, everywhere we can, election security.”
The policy does not give authorization to test state and local government election-related networks or assets – “researchers should follow guidance from those entities for security researcher opportunities and conditions,” according to the report.
“For ES&S products not owned or operated by ES&S, we will accept reports as a result of research under this policy,” the company said.
The vulnerability-disclosure policy also provides safe-harbor language for security researchers. This means that ES&S will not initiative legal action against researchers for “good faith” or accidental violations of the policy. In addition, researchers will be exempt from the Digital Millennium Copyright Act (DMCA), and ES&S said it will not bring a claim against them for circumvention of technology controls.
Finally, researchers would be “exempt from restrictions in our Terms & Conditions that would interfere with conducting security research, and we waive those restrictions on a limited basis for work done under this policy,” according to the policy.
The adoption of safe-harbor language marks a drastic turnaround from how the voting-machine vendor has interacted with the research community in previous years.
At DEFCON in 2018 for instance, ES&S and security researchers butted heads after the company criticized attempts to test voting machines. In a letter to customers, ahead of the conference, ES&S in 2018 also warned election officials that unauthorized use of its software violated the company’s licensing agreements.
Despite this contentious background, security flaws have popped up over the years in the company’s election infrastructure. In 2019, security researchers revealed that they found 35 backend election systems – made by ES&S – that connected to the internet at some point in the past year. And in 2018, the company revealed that it installed remote-access software on some voting machines over a period of six years, raising security concerns.
The announcement also comes during a year when election security is in the spotlight at Black Hat, with the U.S. elections three months away. Security researcher Matt Blaze opened Black Hat 2020 with a call-to-arms for cybersecurity researchers, asking the security space to leverage their expertise to help secure the upcoming U.S. presidential elections, which will likely be a mostly vote-by-mail affair.
Wlaschin for his part said that ES&S has actually been working now with security researchers for at least 18 months – but the program announced on Wednesday formalizes the process. As part of this, ES&S has worked with Synack, a crowdsourced penetration testing platform, to continue to develop its vulnerability disclosure process.
“If you apply [vulnerability disclosure] to our election critical infrastructure, there is a match made in heaven here between security companies and government bodies, and we’re trying to advance that collaboration,” said Mark Kuhr, CTO of Synack.