 LAS VEGAS — The security of social networking sites isn’t as bad as you think. In fact, it’s much worse.
LAS VEGAS — The security of social networking sites isn’t as bad as you think. In fact, it’s much worse.
Sites such as Twitter, Facebook and others that rely heavily on user-generated content, shared content and aggregation have been the targets of increasingly sophisticated attacks over the last few months, and if the problems discussed in a presentation at the DEFCON hacker conference here Saturday are any indication, this is only the beginning.
Two security researchers spent a little less than an hour methodically taking apart the security of these sites, ending with a demonstration of a tool they wrote to implement dynamic cross-site request forgery attacks (CSRF). The tool, called Monkeyfist, gives an attacker the ability to define exactly what data he wants to pull out of a site, what payload to send and which URL to attack. It also can be used to set up one site to attack several others.
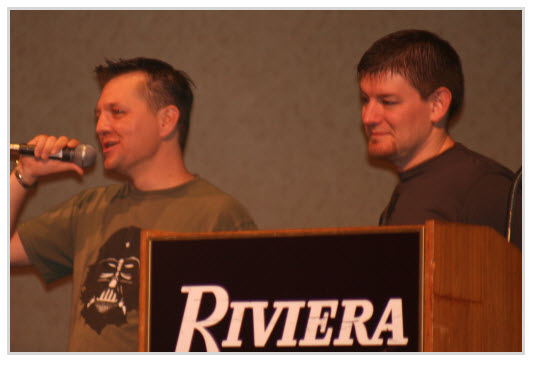
The researchers, Shawn Moyer (above, left) and Nathan Hamiel (above, right), stressed that the very qualities that make social networking sites so popular and easy to use are also what make them easy to attack.
“It’s all of this integration that creates the shared exposure,” said Moyer, a researcher with FishNet Security. “Even if you’re not exposed, you could be exposing someone else.”
CSRF attacks are nothing new and have been well-understood in the security community for a long time. They essentially involve an attacker sending malicious commands from one site to another using the credentials of a user that the destination site trusts. The mitigations for them also are widely known. However, the defenses and mitigations are difficult to get exactly right, especially in today’s Web environment, which relies so heavily on sites trusting one another to share content.
“The mitigations are well-understood, but you have to do lots of things exactly right,” Moyer said. “Most people do most of it, but not all of it.”
But it’s not just social networking sites that have these problems. Any site that relies on user-generated content is likely to run into some kind of CSRF issue. In their demonstration, Moyer and Hamiel used Monkeyfist to edit the Wikipedia entry on CSRF using a CSRF attack. They added the section titled “Other Approaches to CSRF.”
“It’s all about attacker return on investment. You don’t need remote code execution to get ROI,” Hamiel said. “Multisite aggregation is attacker ROI.”









