Three suspected members of the FIN7 cybercrime group have been arrested in Europe and accused of hacking more than 120 U.S.-based companies with the intent of stealing bank cards.
In total, U.S. Department of Justice authorities said the FIN7 group — associated with the Carbanak crime gang — is responsible for the loss of tens of millions of dollars.
The three suspects are Fedir Hladyr, Dmytro Fedorov and Andrii Kolpakov, all arrested in the first half of the year. According to a court filing released Wednesday, Hladyr is in U.S. custody in Seattle, and the two remaining suspects are facing an extradition request by the D.O.J: Kolpakov remains in Spain and Federov is in Poland.
All three were identified as Ukrainian nationals and charged with 26 felony counts of alleged conspiracy, wire fraud, computer hacking, access device fraud,and aggravated identity theft, according to the U.S. Attorney’s Office of the Western District of Washington that is handling the case.
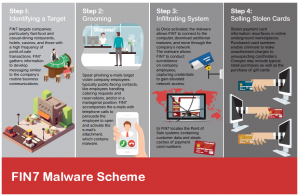
Since 2015, FIN7 has focused on point-of-sale targets at casual-dinning restaurants, casinos and hotels. The group typically uses malware-laced phishing attacks against victims in hopes they will be able to infiltrate systems to steal bank-card data and sell it. The group is known for its innovation when it comes to developing unique attack techniques and cycling through them before adequate defenses could be mounted.
“Throughout 2017, FIN7 was observed creating novel obfuscation methods, and in some cases modifying the methods on a daily basis while launching attacks targeting multiple victims,” wrote FireEye in its technical analysis of the criminal group posted Wednesday. “The threat group regularly tested malicious .Doc, .DocX, and RTF phishing documents against public repositories to check static detection engine coverage.”
In April, Hudson Bay, the parent company of Saks Fifth Avenue and Lord & Taylor, suffered a major breach of the company’s payment systems. The breach was attributed to FIN7 by Check Point security researchers, who said the FIN7 attackers managed to steal credit- and debit-card information for about 5 million shoppers.
Last summer, FIN7 was identified as the group behind a series of attacks against restaurants across the United States. The objective was to seize system control and install a backdoor to steal financial information at will, using a clever exfiltration technique involving DNS queries.
The court documents also mention Chipotle Mexican Grill, Chili’s, Arby’s, Sonic Drive-In and Red Robin as being among the group’s victims.
“These malicious actors are members of one of the most prolific financial threat groups of this decade, having carefully crafted attacks targeted at more than 100 organizations,” wrote FireEye.
FireEye was careful to note: FIN7 is referred to by many security vendors as Carbanak, “although we do not equate all usage of the Carbanak backdoor with FIN7.” Besides the point-of-sale attacks, the Carbanak gang is known for targeting internal banking infrastructure and ATMs.
“The individuals we charged were involved in targeted phishing attacks that may have been used to target 100 companies here in the United States and around the world,” said Annette Hayes, U.S. Attorney for the Western District of Washington. “From there, they used malware tools to reach into more than 3,600 business locations across the country that involved the loss of over 15 million payment cards.”
She added that the group has international reach and also has targeted business in the U.K., Australia and France.
The indictment alleges: “FIN7 used a front company, Combi Security, purportedly headquartered in Russia and Israel, to provide a guise of legitimacy and to recruit hackers to join the criminal enterprise. Combi Security’s website indicated that it provided a number of security services such as penetration testing. Ironically, the sham company’s website listed multiple U.S. victims among its purported clients.”