Criminal fantasy dream-site Webstresser[.]org, a DDoS-for-hire market believed to be behind at least 4 million cyberattacks around the world, has served up its last internet-paralyzing traffic tsunami.
A multi-national investigation led by Europol has led to the arrest of the administrators of the site, which sold the capability to knock websites offline and take down domains for as little as $18 per month.
The appropriately named Operation Power Off, led by the Dutch National High Tech Crime Unit and the UK’s National Crime Agency, with the support of Europol, the FBI and a dozen law enforcement agencies from around the world, also shut down the service completely and seized its infrastructure, which was installed in the Netherlands, the US and Germany.
The administrators were located in the Canada, Croatia, Serbia and the United Kingdom, and further measures were taken against the top users of marketplace in Australia, Canada, Croatia, Hong Kong, Italy, the Netherlands, Spain and the United Kingdom, according to Europol.
Webstresser, which Europol bills as the world’s biggest DDoS-for-hire marketplace, had more than 136,000 registered users, who carried out a combined 4 million attacks as of April 2018.
The rise of cheap DDoS-as-a-service has lowered the barrier to entry for would-be cybercriminals and hacktivists to get into the website-blocking game, so the demise of Webstresser is sure to send a few shock tremors across the underworld landscape.
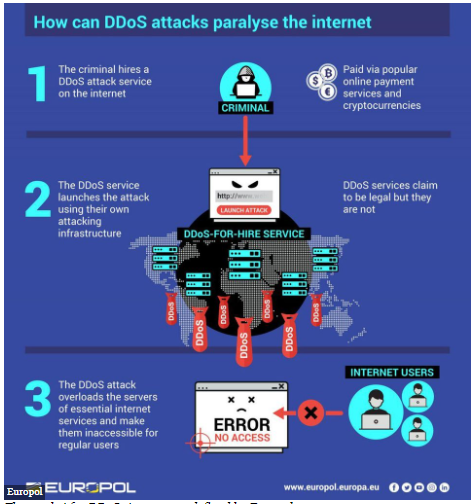 “It used to be that in order to launch a DDoS attack, one had to be pretty well-versed in internet technology. That is no longer the case,” said Europol. “With webstresser[.]org, any registered user could pay a nominal fee using online payment systems or cryptocurrencies, to rent out the use of stressers and booters. Fees on offer were as low as EUR 15.00 a month, thus allowing individuals with little to no technical knowledge to launch crippling DDoS attacks.”
“It used to be that in order to launch a DDoS attack, one had to be pretty well-versed in internet technology. That is no longer the case,” said Europol. “With webstresser[.]org, any registered user could pay a nominal fee using online payment systems or cryptocurrencies, to rent out the use of stressers and booters. Fees on offer were as low as EUR 15.00 a month, thus allowing individuals with little to no technical knowledge to launch crippling DDoS attacks.”
Unsurprisingly, the frequency of attacks has increased.
“The latest Corero DDoS Trends Report continues to show that our average customer is attacked six times per day,” Andrew Lloyd, president at DDoS specialist Corero Network Security, said via email. “We strongly suspect that the widespread use of rented attacks contributes to the fact that 73 percent of attacks last less than 10 minutes; why pay for a longer attack than you need? It remains ridiculously cheap to rent a devastating DDoS attack from these so-called DDoS stressers or on the Dark Web.”
Bromium CEO Gregory Webb told Threatpost that there are on average 6.5 million DDoS attacks per year, each reaping significant financial gain for the bad actors behind them: DDoS attacks-for-hire generate $13 million in revenue per year, he said. Meanwhile, the average DDoS attack costs a business around $200 per day, with some rising to as much as $1,000 per day.
“The platform criminality model is productizing malware and making cybercrime as easy as shopping online,” he said in an email interview. “Not only is it easy to access cybercriminal tools, services and expertise: It means enterprises and governments alike are going to see more sophisticated, costly and disruptive attacks as ‘the web of profit’ continues to gain momentum.”
And that’s why there are likely to be other sites rising to take Webstresser’s place. They’re difficult to disrupt, since many of these bill themselves as “testing” services, for legitimately gauging a website’s resiliency to, you guessed it, DDoS attacks.
“Stressers in general are looking to make money under the guise of offering a legitimate and useful service when, in reality, most of them require no proof of identity of the individual launching the attack or that they are indeed associated with, or have the approval of, the organization that is the subject of the attack,” Sean Newman, director of product management at Corero, said via email. “Legitimate penetration testing companies are available for any organization that genuinely wishes to test their security preparedness.”










