The GandCrab ransomware group is shutting down, according to posts on the Dark Web.
Researchers David Montenegro and Damian spotted the announcements over the weekend.
https://twitter.com/CryptoInsane/status/1134727041826377729
Noting that “all good things come to an end,” GandCrab’s operators in a posting on the exploit[.]in underground market claim the malware has raked in nearly $2 billion since the ransomware launched in January of last year. That encompasses ransomware-as-a-service (RaaS) earnings as well as $150 million for the operators themselves. They said they were averaging $2.5 million per week.
Yet, despite all of this success – and perhaps due to more GandCrab decryptors popping up to help businesses combat infections – the group said that it is suspending their servers, ads and infrastructure.
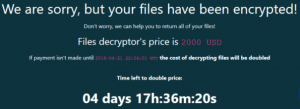
The operators also warned, “Victims, if you buy, now. Then your data no one will recover. Keys will be deleted.”
Michael Gillespie, Emsisoft researcher and creator of the ID Ransomware service, told Threatpost: “The number of GrandCrab submissions to ID Ransomware has been trending downwards for some time. I think they’re doing like the TeslaCrypt devs; getting out while the going is good and sailing away on their yachts. Unfortunately, no-one will ever be able to decrypt unless the criminals release the keys for the more recent variants.”
GandCrab: A Swiftly Moving Malware
GandCrab is a fairly standard ransomware in that it scans infected Windows systems and any network shares for files to encrypt. It’s recognizable by the “.gdcb” extension that it appends to encrypted files.
Yet in the 16 months since its debut, it has become one of the most prolific ransomware strains out there, as GandCrab’s operators have also continued to evolve its code (there are five versions) and infection vectors.
Those operators specialized in the RaaS model, according to researchers, and partnering with botnet operators and other affiliate cybercriminals – which helps account for its widespread virulence. It spreads in various ways, including via spam emails, exploit kits, targeted social engineering efforts, fake software downloads and malicious websites; and it was recently spotted as the final payload for a series of attacks that exploit the recently patched, critical Oracle WebLogic bug, CVE-2019-2725.
Some attackers have customized the code as well; recently for example Bromium identified a new PowerShell technique being used to spread GandCrab that uses Excel documents and an image of Super Mario to infect machines. It only attacked Windows computers in Italy, and was coded to not execute if the infection landed in a different geography.
“Analysis showed PowerShell code launching from malicious Excel spreadsheets, which are freshly rewrapped to avoid detection by signature-based security tools,” Bromium explained in its blog on the campaign, in May. “The script is then used to download a picture of Super Mario which contains more PowerShell code that ultimately downloads GandCrab ransomware, encrypting files and network assets. By hiding the ransomware within images, it makes it nearly impossible for perimeter detection to work out if there is something malicious within the code.”
Despite their successful 16-month run, GandCrab’s operators are ready to retire, they said.
“We successfully cashed this money and legalized it in various spheres of white business,” they posted. “We are leaving for a well-deserved retirement. We have proven that by doing evil deeds, retribution does not come. We proved that in a year, you can earn money for a lifetime.”