Developers behind the malicious downloader Hancitor have bolstered the malware again, this time with new delivery approaches that make it more difficult to detect.
The downloader is still spread through malicious attachments, and distributing malware designed to steal data, such as Pony and Vawtrak, but researchers said the way that Hancitor’s payload is delivered is different than from previous iterations.
Two FireEye researchers, Ankit Anubhav and Dileep Kumar Jallepalli, said the downloader has shifted to using a three-pronged delivery approach, and explained the updates in a blog post on Friday.
One technique involves using an uncommon but native Windows API, “CallWindowProc,” to execute shellcode. The second method piggybacks on the previous technique and relies on another API callback function, “EnumResourceTypesA,” to interpret and execute shellcode. As the researchers note, macros can call APIs directly, but it’s not often they run shellcode.
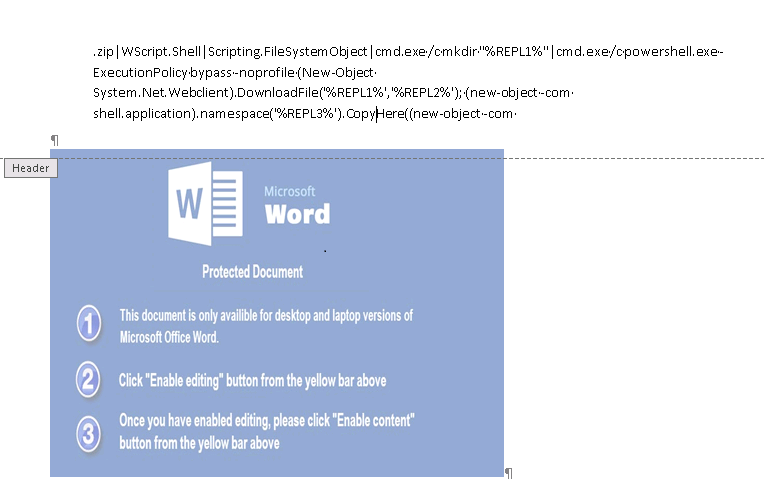
The third and perhaps most interesting technique is rooted in Hancitor’s ability to obscure malicious PowerShell commands. When users are tricked into enabling macros, they can also open the door to PowerShell command creation, researchers said.
The malware combines code fragments – taken from the section_header of the embedded image – to assemble the command. The attackers use a tiny font, size 1, to obscure the PowerShell text, making it even more difficult to notice, researchers claim.
From there the PowerShell obtains a payload from the attacker-controlled website in .ZIP format and uses a function to unzip it.
Assembling a PowerShell command on the fly like this is an excellent way to evade basic standard methods of detection, usually applied to macros forms, the two write.
After downloading the executable, code deletes the archive to remove any trace of it, and executes it to download the Pony password stealer and the Vawtrak Trojan.
This iteration of the Pony stealer allows for the theft of autocomplete Intelliforms data, such as passwords stored in Internet Explorer’s system registry, in addition to passwords saved in Firefox. According to Anubhav and Jallepalli code is also present in Pony that allows for the theft of Microsoft Outlook data.
Hancitor has been around for about two years but disappeared for a spell last year. Researchers with Proofpoint determined that Hancitor was back from its lengthy hiatus in May and was pushing Pony and Vawtrak.
Researchers from Palo Alto Networks corroborated that stance in August, noting that one variant it saw was using native API calls within Visual Basic – “CallWindowProcA” – to decrypt embedded malware from Word documents.
That Hancitor was relying on embedded executables, something that normally trips antivirus programs, was of interest to Ryan Olson, a researcher on Palo Alto’s Unit 42 at the time.
“When you have embedded code inside an Office document you open up more risk of being detected by an antivirus program,” Olson told Threatpost in August, “with Hancitor the code is embedded in the VB that encrypts it in a way that the AV isn’t going to find it.”
To better evade detection, it appears Hancitor’s authors have elected to stick with the CallWindowProc API – it’s clearly working – and add another API (“EnumResourceTypesA”) and a PowerShell command.
While delivery of the payload has evolved over the last few months, the malware is still being spread through malicious attachments in phishing emails purporting to be invoices, researchers claim. Like many forms of malware these days, unsuspecting victims still have to enable macros to get infected. From there, it downloads and executes Hancitor before going on to drop the additional information stealing payloads.