LAS VEGAS – More hospitals are adopting internet of things (IoT) devices, from wearables to smart insulin pens. But neither hospitals nor the device manufacturers themselves are ready to address the onslaught of security and privacy challenges that come with medical connected devices.
At least 82 percent of connected medical devices have been targeted in the past year, opening the potential for a variety of attacks, from highly-sensitive information disclosure to denial of service (DoS) for critical devices, a recent Xtelligent Healthcare Media survey found.
“There are drivers across the industry that are putting facilities and patients at risk,” said Ferdi Steinmann, industry strategist for life sciences at OpenText, speaking at the ENFUSE 2019 event in Las Vegas this week. “The growth in devices, an aging population and regulatory compliance all are creating a lot of headache for access control and security solutions.”
Amid an aging U.S. population and rising healthcare costs, more telehealth solutions – using connected devices like connected inhalers and Apple Watch monitoring apps – are coming to market to help doctors collect data on patients who may live in rural areas without hospitals, or elderly patients who can’t travel. In fact, while the telehealth market was valued at $49.8 billion in 2018, that valuation is estimated to potentially reach $266.8 billion by 2026.
“The telehealth market will significantly expand due to the ability to reach the rural population and aging population,” said Steinmann.
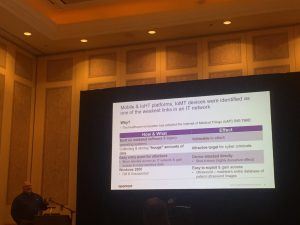
IoT Medical Device Issues
As more and more medical devices become connected, more security issues are popping up. Last year, researchers found vulnerabilities in pacemaker programmers (Carelink 2090) and insulin pumps (models like the MiniMed 508) made by manufacturer Medtronic, while in April, a slew of devices from medical technology company Becton Dickinson and Co. (BD) were found to be vulnerable to the infamous KRACK key-reinstallation attack, potentially enabling hackers to change and exfiltrate patient records.
Widespread security issues exist at the manufacturing level when it comes to medical IoT devices. For instance, many devices use the same hardcoded administrative passwords to permit privileges access across multiple devices; passwords which cannot be changed by users or even the facility’s system administrator.
In addition, some medical connected devices come with no authenticated access – so while administrative accounts can be used by service technicians for device management, no authentication is required for regular user access.
On the manufacturing end, enforcement of basic security principles is increasingly on the table. For instance, this several laws are being proposed across the world: The closest of these to become law in the U.S. is the California Senate Bill 327 (SB-327), which would require “reasonable security feature or features that are appropriate to the nature and function of the device.”
SB-327 was first proposed in 2018 and will become law in January 2020. While the bill has drawn backlash from the security community for not going far enough, researchers said that “it mandates reasonable security features for smart-tech manufacturers,” such as enforcing unique passwords for IoT devices.
But in the meantime, manufacturers need to focus on an array of security aspects with connected devices, including selecting their base hardware carefully (make sure the chip has secure storage, a lockable bootloader, toolchain access, etc.), ensuring that firmware and software is developed by developers who can demonstrate good security expertise, and getting third-party advice early on.
Diagnosing Medical Security Issues
Beyond manufacturer vulnerabilities in the devices themselves, security issues exist across the board. Healthcare companies are using outdated software and legacy operating systems (including Windows XP) and collecting huge amounts of data without securing it. Just last month, four healthcare IT companies warned that ProCare Health had been storing hundreds of thousands of patient records containing personally identifiable information (PII) – without the knowledge or consent of the data subjects.
The consequences can be significant. A recent study found that healthcare has the highest average cost-per-capita for a data breach, at $408 (with pharmaceutical companies having the fourth-highest average cost), according to Steinmann. The implications of attacks on healthcare are also seen in the WannaCry ransomware attacks of 2017 which spread to more than 300,000 computers in 150 countries – hitting hospitals and the National Health Service in the UK particularly hard. These attacks not only brought down computer systems, but paralyzed hospitals’ ability to keep customers’ appointments, preventing patients’ access to care.
Hospitals and healthcare centers, which have notoriously lax culture when it comes to security, need to take an “outside in access” approach when it comes to securing connected medical devices that are used and deployed by hospitals to patients. That is, the level of access and the risk should be categorized for each device, said Steinmann.
“An Identity Access Model (IAM) needs IT staff, security staff, but also stakeholders who can think about not just the users, but the devices being used – that needs to be considered upfront,” he said.
What are the top risks to modern enterprises in the peak era of data breaches? Find out: Join breach expert Chip Witt from SpyCloud and Threatpost senior editor Tara Seals, in our upcoming free Threatpost webinar, “Trends in Fortune 1000 Breach Exposure.” Click here to register.