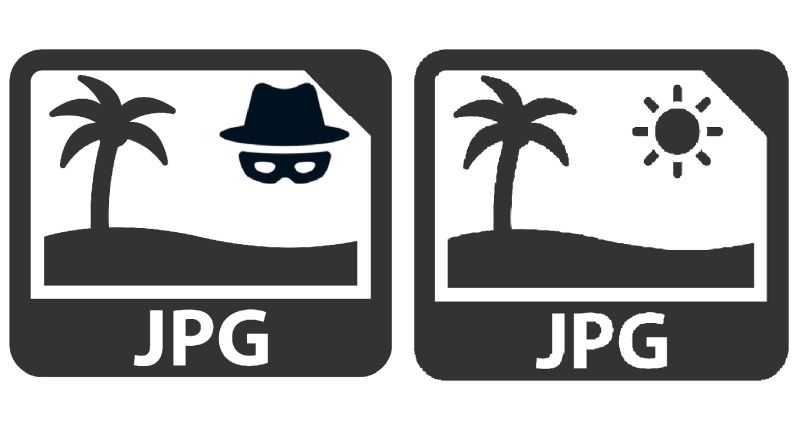
Magecart attackers have found a new way to hide their nefarious online activity by saving data they’ve skimmed from credit cards online in a .JPG file on a website they’ve injected with malicious code.
Researchers at website security firm Sucuri discovered the elusive tactic recently during an investigation into a compromised website using the open-source e-commerce platform Magento 2, Luke Leal from Sucuri’s malware research team said in a report posted online last week.
“The creative use of the fake .JPG allows an attacker to conceal and store harvested credit card details for future use without gaining too much attention from the website owner,” he wrote.
Peering under the hood of the compromised site revealed a malicious injection that was capturing POST request data from site visitors, Leal explained. “Located on the checkout page, it was found to encode captured data before saving it to a .JPG file,” he wrote.
A POST request method asks a web server to accept data enclosed in the body of the request message, usually so it can be stored. It’s often used in Web transactions when someone has uploaded a file to a website or submitted a completed web form.
Specifically, Sucuri found that attackers injected PHP code into a file called ./vendor/magento/module-customer/Model/Session.php, then used the “getAuthenticates” function to load malicious code, Leal said. The code also created a .JPG file, which attackers used to store any data they captured from the compromised site, he said.
“This feature allows the attacker to easily access and download the stolen information at their convenience while concealing it within a seemingly benign JPG,” Leal wrote.
Indeed, threat actors aiming to steal data from online transactions are constantly trying to find new ways to evade detection by concealing their activity in creative ways.
Magecart attackers–different threat groups who all compromise e-commerce websites with card-skimming scripts on checkout pages to steal customer payment and personal data–are particularly adept at this activity. They often hide their skimming techniques in functionality that appears authentic as well as use the platforms they attack to cannibalize themselves to achieve their results.
A Magecart campaign discovered around Christmastime, for instance, concealed itself within convincing PayPal iframes in the PayPal checkout process of e-commerce sites to steal user credentials and credit-card info.
The latest campaign also leveraged the Magento code framework to do its dirty work of harvesting the data captured and hidden in the .JPG file, Leal explained. The malicious PHP code relied on the Magento function “getPostValue“ to capture the checkout page data within the “Customer_ POST parameter,” he said.
It also used the Magento function “isLoggedIn” to check whether a victim is logged into the site as a user and, if this was the case, attackers also lift the user’s email address from the transaction, he said.
“Nearly all of the information submitted by the victim on the checkout page is stored within the ‘Customer_ parameter,’ including full names and addresses, payment card details, telephone numbers, and user agent details,” he wrote.
Once attackers get their hand on customer payment data, they can then go on to use it for various criminal activities, such as credit-card fraud or targeted e-mail-based spam or phishing campaigns, Leal added.
While this latest Magecart anti-detection approach may make the infection difficult to initially spot, it would help website owners to identify new files in the environment or detect potentially malicious changes before they do damage if they implement website monitoring services or integrity control checks, Sucuri recommended.
Check out our free upcoming live webinar events – unique, dynamic discussions with cybersecurity experts and the Threatpost community:
- March 24: Economics of 0-Day Disclosures: The Good, Bad and Ugly (Learn more and register!)
- April 21: Underground Markets: A Tour of the Dark Economy (Learn more and register!)