Microsoft has issued fixes for 36 CVEs for December 2019 Patch Tuesday across a range of products, with seven of them rated critical in severity – and one that’s already being exploited in the wild as a zero-day bug.
The computing giant’s scheduled security update this month is relatively light, and includes patches for Microsoft Windows, Internet Explorer, Microsoft Office and related apps, SQL Server, Visual Studio and Skype for Business. In all, December Patch Tuesday addressed seven bugs that are rated critical, 28 that are rated important, and one that rated moderate in severity.
Zero-Day Bug Exploited in the Wild
CVE-2019-1458 is an elevation-of-privilege vulnerability in Win32k, which has a live zero-day exploit circulating in the wild. The exploit allows attackers to gain higher privileges on the attacked machine and avoid protection mechanisms in the Google Chrome browser, researchers said.
“An attacker could exploit the flaw to execute arbitrary code in kernel mode on the victim’s system,” said Satnam Narang, senior research engineer at Tenable, via email. “From there, the attacker could perform a variety of actions, such as creating a new account with full user rights, installing programs, and viewing, changing or deleting data.”
The one caveat is that to exploit the flaw, an attacker would need to have previously compromised the system using another vulnerability – thus, it’s rated only as important in severity and carries a CVSSv3 base score of 7.8 out of 10. However, since it has been exploited in the wild as a zero-day, IT security staff should prioritize the patch, researchers said.
“This is one of many vulnerabilities that Microsoft resolved in 2019 that were being exploited but were not rated as a critical severity,” said Chris Goettl, director of product management, Security, at Ivanti, via email. “If your vulnerability-management criteria use vendor severity or CVSS score as criteria for determining what should be updated, you should re-evaluate your criteria to ensure exploited vulnerabilities like this do not slip past your prioritization process.”
The zero-day was found by Kaspersky researchers as a result of a separate zero-day exploit for Google Chrome that was seen in November, being used to execute arbitrary code on a victim’s machine. The newly discovered Windows EoP was embedded into a previously discovered Google Chrome exploit, the firm said: “It was used to gain higher privileges in the infected machine as well as to escape the Chrome process sandbox – a component built to protect the browser and the victim’s computer from malicious attacks.”
The exploits are being used by a threat group called “WizardOpium.”
Microsoft has addressed the vulnerability by correcting how Win32k handles objects in memory. The flaw is also similar to the CVE-2019-0859 bug reported in April, for which an exploit was developed and found being sold on underground markets.
Critical Bugs
In terms of the critical bugs included in this month’s Patch Tuesday, a critical remote code-execution (RCE) vulnerability in Win32k Graphics (CVE-2019-1468) would allow an adversary to create a new account with full user rights, install programs, and view, change or delete data. It exists due to the Windows font library improperly handling specially crafted embedded fonts. Attack vectors would be via a malicious document, or by luring users to a specially crafted website containing the exploit code.
“To exploit the vulnerability, an attacker would need to run a specially crafted application on the guest operating system, resulting in execution of arbitrary code on the host operating system,” said Narang.
Also on the RCE front, critical-rated CVE-2019-1471 in Windows Hyper-V exists due to improper validation of inputs from an authenticated user on the guest operating system by the host server.
“This critical-rated patch fixes a bug in Hyper-V that would allow a user on a guest OS to execute arbitrary code on the underlying host OS,” explained Dustin Childs, researcher with Trend Micro’s Zero-Day Initiative. “Bugs like this have been demonstrated at Pwn2Own in the past, and they’re always fun to watch. Considering how much modern computing depends on virtualization, it’s likely we’ll continue to see research that focuses on exploiting the hypervisor from a guest OS.”
Microsoft also announced five critical vulnerabilities for Microsoft’s Git for Visual Studio 2017 and 2019 (CVE-2019-1349, CVE-2019-1350, CVE-2019-1352, CVE-2019-1354, CVE-2019-1387).
The description for all of them is identical: an RCE bug that exists when Git for Visual Studio client improperly sanitizes input (sanitization is the process of modifying input to ensure that it is actually valid).
“As Visual Studio is one of the most popular development environments used today to design and build applications, this exploit puts engineering organizations on the front lines of a potential attack,” explained Richard Melick, senior technology product manager at Automox, via email. “If left unpatched, engineering and development groups would be at risk to being the point of entry for malware deployment, lateral movement through the network, rogue account creation, and theft of proprietary application code.”
In order to exploit any of these Visual Studio vulnerabilities, an attacker would need to use the Git client to download a malicious repository to the victim’s endpoint.
“While not common, it is still possible using fairly simple techniques,” Melick said. “By running intelligence gathering in channels like LinkedIn and job listings, an attacker could learn about an organization’s use of Visual Studio and the details of the open-source projects in play. From there, entry into the network could come through a common phishing email technique to the engineering for help troubleshooting a compatibility issue with their open-source software, providing a link to the Git repository, or even for an interview as an example of previous work. The engineering team would then download the malicious repo, allowing the malicious code to execute, giving attacker access.”
Additional Notes
One other bug that stood out to researchers in the update is CVE-2019-1469, an important-rated Win32k information disclosure vulnerability that exists when a Win32k component improperly provides kernel information.
“A successful attack through this vulnerability could result in private data being revealed to an attacker, providing necessary information to further compromise the victim’s system,” Melick said. “A successful attack relies on access to the machine to load a specially crafted application.”
And finally, it’s also worth mentioning that there is only one Patch Tuesday left (in January) until Windows 7 and Server 2008\2008 R2 reach end-of-life and Microsoft stops issuing security fixes for them.
“There is no doubt we are going to see a similar situation to the Windows XP end-of-service with a large number of these machines still in use and not updated,” Melick said. “It is safe to assume that many of these machines in this bucket are falling under unmanaged or mission-critical categories with no clear path to update.”
Also on Patch Tuesday, Adobe issued 17 critical vulnerabilities in Acrobat Reader, Photoshop and Brackets, which could lead to arbitrary code execution if exploited.
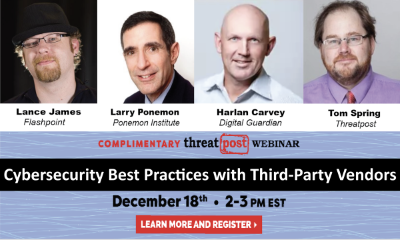
Free Threatpost Webinar: Risk around third-party vendors is real and can lead to data disasters. We rely on third-party vendors, but that doesn’t mean forfeiting security. Join us on Dec. 18th at 2 pm EST as Threatpost looks at managing third-party relationship risks with industry experts Dr. Larry Ponemon, of Ponemon Institute; Harlan Carvey, with Digital Guardian and Flashpoint’s Lance James. Click here to register.