Researchers have spotted a variant of the Dridex banking trojan with new obfuscation capabilities that help it skirt anti-virus detection.
While Dridex has been around since 2011, researchers told Threatpost Friday that they recently spotted phishing emails distributing a never-before-seen variant of the malware. This variant uses file signatures that are difficult for anti-virus software to sniff out – allowing the malware to evade detection when on infected systems.
JR DePre, red team technical manager with eSentire, told Threatpost that the new vartiant is another step in the “constant game of cat-and-mouse” being played between defenders and attackers behind the Dridex malware: “As detection for new techniques continues to evolve, the malicious actors will continue to update their tools to bypass those detections.”
“Due to the popularity of Dridex within modern attacks, it’s safe to assume that the developers of the malware will continue to advance their techniques,” said DePre.
Dridex first appeared in the wild in 2011 – but in the almost decade since, the malware has undergone a series of transformations. Researchers said in a Thursday analysis that like infamous banking trojan Emotet, “each new version of Dridex traces a further step in the global arms race as the security community responds with new detection and mitigations.”
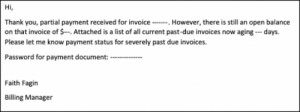
Most recently, researchers spotted the malware being delivered to victims via an email in the form of a malicious document with embedded macros. Once downloaded, Dridex then targets banking information.
“Depending on the environment, the macros can be triggered by varying levels of employee interaction,” said researchers. “The message in the email appears… with specific numbers redacted (as they could potentially be used by a threat actor to track campaign victim metrics).”
The new variant in this phishing email came with several key changes: The biggest of which are tactics aimed at avoiding anti-viral detection.
Anti-virus software mainly rely on file signatures (MD5 or SHA256 hashes) to detect malicious applications, DePre explained. Dridex utilizes newly created and signed 64-bit dynamic link libraries (DLLs), which have different file signatures from previous versions that have been detected by anti-virus software in the past.
“These DLLs are side loaded via legitimate MS Windows binaries, making them appear to be part of a legitimate software product, and thus more difficult to detect,” DePre told Threaptost.
The new feature is proving effective: So far, only 19 anti-virus products (of about 60) have identified the trojan’s behavior. A full list of the anti-virus engines that successfully detected the trojan – and those that haven’t – can be found on VirusTotal.
In another novel change, the malware also utilizes an Application Whitelisting technique to bypass mitigation techniques, showing another attempt by the the malware authors to trip up defense tactics.
This tactic takes advantage of a weakness in the WMI command-line (WMIC), a software utility that enables users to carry out Windows Management Instrumentation operations with a command prompt. Windows Management Instrumentation is the infrastructure for management data and operations on Windows-based operating systems.
Specifically, the malware targets a weak execution policy in the WMIC’s application whitelisting process around XLS scripts. Application whitelisting is the process of specifying approved applications that are permitted to be executed within a computer environment; many companies utilize this technique to protect themselves from harmful applications.
The weakness means that XLS scripts containing malicious Visual Basic Script (VBS) can be loaded: “Essentially, if a company has Windows Script host disabled or blocked, this variant can bypass that whitelisting technique and still execute malicious code via WMIC using a XLS file with malicious VBS in it,” said DePre.
Researchers told Threatpost that they don’t have any further information at this time about the threat actor behind Dridex but “are continuing investigations.”