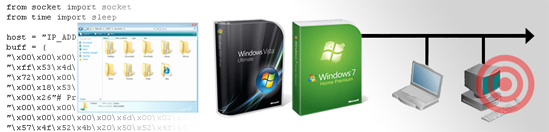
Researchers have found a new vulnerability in the SMB2 protocol in Windows Vista and Windows 7 that enables an attacker to remotely crash vulnerable machines. There is proof-of-concept exploit available for the vulnerability, as well.
There is no patch available for the vulnerability, which affects fully updated machines running all versions of both 32-bit and 64-bit Windows Vista and Windows 7. SMB2 is a newer version of the venerable Server Message Block protocol. The suggested workaround for defeating the exploit is to disable SMB2 until a patch is available.
On Tuesday, Microsoft released an advisory on the SMB2 problem, confirming the vulnerability and saying that the issue with Windows 7 exists only in the Windows 7 Release Candidate and not in the Windows 7 RTM.
From the vulnerability bulletin:
SRV2.SYS fails to handle malformed SMB headers for the NEGOTIATE PROTOCOL REQUEST functionality.
The NEGOTIATE PROTOCOL REQUEST is the first SMB query a client send to a SMB server, and it’s used to identify the SMB dialect that will be used for further communication.
In order for the attack to work, file sharing must be enabled on the target machine. The researcher who discovered the flaw, Laurent Gaffie, said that he has contacted Microsoft and notified them of the vulnerability. News of the flaw comes on the monthly Patch Tuesday for Microsoft, a day on which the company will be releasing five critical fixes for its products.
SMB2 was designed by Microsoft as a more efficient and modern version of the original SMB protocol, which was designed by IBM. SMB is used for sharing resources such as printers, files and ports across a network.