The realistic approach to security is that incidents occur. While ideally, the CISO would want to prevent all of them, in practice some will succeed to a certain degree—making the ability to efficiently manage an incident response process a mandatory skill for any CISO. Moreover, apart from the management of the actual response process, the CISO must also be able to efficiently communicate the ongoing activities and status to the executive level.
While the IR process is mostly technical, reporting to the organization’s management should take place on a much higher level in order for the non-security -savvy executives to understand. To assist CISOs with these tasks, Cynet created the IR Management and Reporting PowerPoint template (download here) which apart from providing an actionable response framework, is also clear and intuitive for the executive level.
Let’s drill down on the two aspects of the template:
IR Management
The template was built on the SANS\NIST framework which includes the following stages:
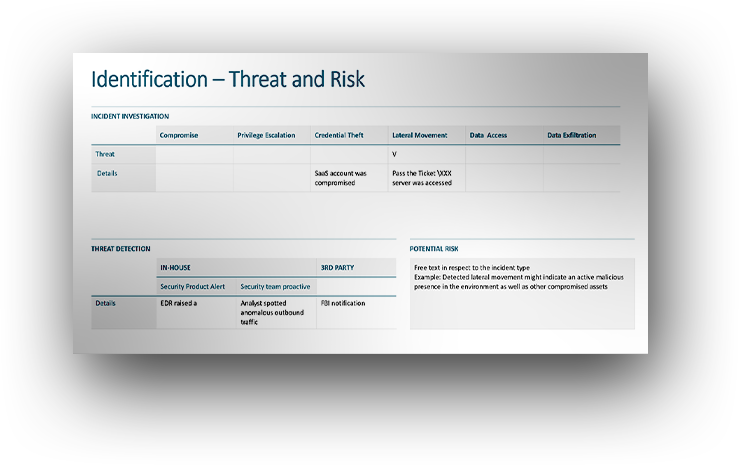
- Identification
This stage includes all activities that relate to the initial discovery of malicious presence and activity. It covers a wide range of potential scenarios – discovery carried out by the internal security team or by an external entity, was it in the context of the standard security protocols or a mere coincidence. This stage includes also an initial risk estimation for onward steps.
- Containment
Following the initial identification, there is a critical need for immediate action to confront and mitigate the discovered threat—prior to any further investigation of root cause and scope. Once this mitigation is carried out, onward steps can be calculated.

- Eradication
This stage refers to the full scope of the investigation to determine where did the attack originate from and to what extent was it successful. This investigation should be concluded by ensuring that any malicious activity, presence, and infrastructure are totally removed. - Recovery
After the eradication stage, outline all activities that entail restoring operations back to routine, relating to IT entities (servers, laptops, desktops, user accounts, apps, and cloud workloads) and data resources backup. - Lessons Learned
This is the slide where you draw actionable conclusions from the attack in terms of enhancing the environment resilience, reducing attack surfaces, and potentially making additional security investments.
IR Reporting
To turn the security process more digestible for management the template focuses on two key themes – actions taken to control the incident and continuous insights into its root cause and scope. Both are required for clear risk perception of the event.
The control aspect gained through striving for as much transparency as possible regarding what in the attack is already known and what is yet to be discovered as well as mapping out the knowledge gains and gaps creates the assurance that the incident is indeed managed.
At the end of the day, the company’s executives operate in the context of operational space – downtime, monetary loss, resources saved or consumed. The template addresses this need by providing a high-level overview of the technical details of the compromise, lateral movement, and fileless techniques to deliver a translation of the incident into the actual and potential damage.
While there are many common denominators to cyberattacks, there are unique qualities for each one. Similarly, there is a high degree of variance between organizations and management types. The template is purpose-built to be broken down and used in a modular manner, customizing it to the specific needs of each organization.
Communication to management is not a nice-to-have part but a critical part of the IR process. The definitive IR Reporting to Management PPT template enables all who work hard to conduct professional and efficient IR processes in their organizations to make their efforts and results crystal clear to their management.
Both management and reporting are essential building blocks in an efficient IR process. The IR Management and Reporting Template attempt to assist the CISO with these tasks – not only perform a top edge response to cyberattacks but also ensure that this professional and critical work is understood and acknowledged.