Python was recently touted as on track to become the world’s most prevalent coding language, looking to swallow, as it were, the majority of the market share for developers. According to recent analysis, Python’s popularity also extends to black hats.
Mirroring the findings around its use by coders overall, Python-based tools were used in up to 77 percent of attacks against sites seen in telemetry from Imperva, between the end of June and mid-September. The data also shows that in over a third of the cases, a Python-based tool was responsible for the majority of daily attacks.
“These levels, over time, show that Python-based tools are used for both breadth and depth scanning,” Imperva said in its report, released Thursday.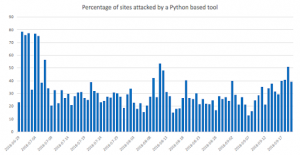
Meanwhile, a survey of GitHub by the firm found that about more than 20 percent of GitHub repositories containing an attack tool or an exploit proof of concept (PoC) are written in Python.
“In virtually every security-related topic in GitHub, the majority of the repositories are written in Python, including tools such as w3af, Sqlmap and even the infamous AutoSploit tool,” Imperva noted.
In a look at web clients, Imperva researchers reviewed their data, specifically security incidents, and found that more than 25 percent of the clients seen — excluding vulnerability scanners – were Python-based tools used by malicious actors, making it the most common vector for launching exploit attempts.
The two most popular Python modules used for web attacks are Urllib and Python Requests, the research found. Use of a new module, Async IO, is just kicking off.
In addition, Python is used to target specific applications and frameworks like Struts and WordPress.
“The advantages of Python as a coding language make it a popular tool for implementing known exploits,” Imperva said. It noted the prevalence especially of exploits for the CVE-2017-9841 PHP-based remote code-execution (RCE) vulnerability in the PHPUnit framework, and CVE-2015-8562 RCE flaw in the Joomla! framework.
“Since Python is so widely used by hackers, there is a host of different attack vectors to take into consideration,” Imperva noted. “Python requires minimal coding skills, making it easy to write a script and exploit a vulnerability.”












