Researchers say they have discovered several major vulnerabilities in the short form video app TikTok. The reported vulnerabilities come as scrutiny around the Chinese-owned platform increases.
Researchers say the most serious vulnerability in the platform could allow attackers to remotely take control over parts of victims’ TikTok account, such as uploading or deleting videos and changing settings on videos to make “hidden” videos public. Researchers also discovered a separate vulnerability that allowed them to obtain personal data of victims, such as email addresses and more.
“Many of us use the TikTok app to share enjoyable moments and snip bits of fun memories in the form of a short video clips,” researchers with Check Point Research said on Wednesday. “But as some have experienced, there is often a fine line between fun clips to private, even intimate assets being compromised while trusting to be under the protection from the apps we use.”
TikTok, a social media app with over 1.3 billion installs worldwide, is owned by Beijing-based parent company ByteDance. The app’s parent company, ByteDance, was notified in November of the flaws and fixed the issue on Dec. 15, researchers said.
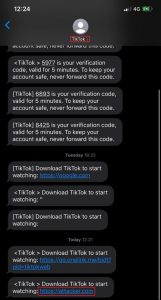
The first vulnerability allowed partial account takeover via SMS link spoofing. Researchers were able to spoof a TikTok SMS link that invites users to download the application.
A potential attacker could send an SMS invite message to a victim by capturing the HTTP request with a proxy tool (such as Burp Suite), inputting the victim’s phone number into the “Mobile” parameter, and changing the “download_url” parameter into a malicious URL of their choosing. The victim would then be sent a legitimate message from TikTok asking them to download the app, with a link to the attacker-controlled malicious domain.
This opens the victim up to an array of attacks, researchers said. “We found that it is possible to send a malicious link to a victim that will result in redirecting the victim to a malicious website. The redirection opens the possibility of accomplishing Cross-Site Scripting (XSS), Cross-Site Request Forgery (CSRF) and Sensitive Data Exposure attacks without user consent,” they wrote.
Researchers found that they could take this attack a step further and send requests on behalf of the user after the victim has opened the URL – enabling them to take over parts of victims’ accounts.
“With the lack of anti-Cross-Site request forgery mechanism, we realized that we could execute JavaScript code and perform actions on behalf of the victim, without his/her consent,” researchers said.
Finally, researchers said that once they had partial control over victims’ accounts, they were able to make several API calls (in the https://api-t[.]tiktok[.]com and https://api-m[.]tiktok[.]com subdomains), which would then reveal sensitive information about the victim including email address, payment information and birthdates.
“TikTok is committed to protecting user data. Like many organizations, we encourage responsible security researchers to privately disclose zero day vulnerabilities to us,” a TikTok spokesperson said in a media statement. “Before public disclosure, Check Point agreed that all reported issues were patched in the latest version of our app. We hope that this successful resolution will encourage future collaboration with security researchers.”
The security flaws come as backlash swells around TikTok’s relationship with China, leading the United States Army this week to announce that U.S. soldiers can no longer have the social media app on government-owned phones.
Concerned about mobile security? Check out our free Threatpost webinar, Top 8 Best Practices for Mobile App Security, on Jan. 22 at 2 p.m. ET. Poorly secured apps can lead to malware, data breaches and legal/regulatory trouble. Join our experts to discuss the secrets of building a secure mobile strategy, one app at a time. Click here to register.