It’s a familiar refrain: Attackers often have months of unfettered access to corporate networks; and security and network managers remain in the dark until they’re notified of serious breaches by third parties.
Enterprises, regardless of industry, dread that fateful knock on the door by the FBI, card brands or fraud detection services informing them that an external group has been moving data off their network for months. Yet it’s happening with greater frequency and with devastating consequences in some cases, according to the 2013 Verizon Data Breach Investigations Report (DBIR).
This year’s version of the DBIR has quantified not only financially motivated attacks, but also those carried out by state-sponsored attackers targeting intellectual property or military secrets. The numbers in the report paint a representative picture of the state of affairs for companies that value IP such as those in manufacturing and telecommunications, and the numbers aren’t pretty. Sixty six percent of breaches remain undiscovered for months or longer, up from 55 percent in 2011 and 41 percent in 2010.
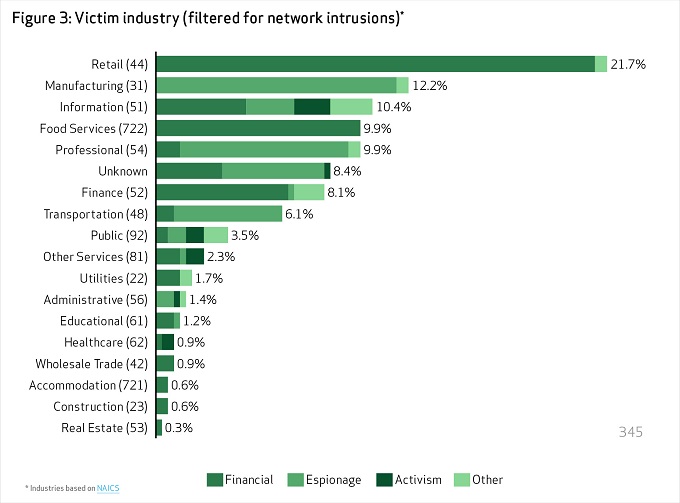
Targeted attacks and attacks motivated by espionage represent 21 percent of the 621 breaches investigated by Verizon’s RISK Team and those attacks account for the inflated numbers representing the time from initial compromise to discovery, Verizon said.
“That pits the virtually unlimited resources of a nation against the very finite resources of a single company. Nobody can reasonably be expected to withstand that,” the DBIR says, adding that while prevention remains an important part of any security strategy, more investment must be made in detection and response to breaches that result in data loss.
This year’s report paints a gruesome picture, one where most companies are compromised and lose data in a matter of hours. Financially motivated attacks that rely on relatively simple SQL injection attacks or compromises of remotely accessible point-of-sale systems guarded by weak or default credentials beef up those numbers substantially. Attackers are able to break those systems in a matter of seconds or minutes. And initial compromises in financially motivated attacks are not difficult, according to the DBIR data. In such attacks, 78 percent were considered low or very low difficulty, while in espionage-related attacks, the degree of difficulty climbs to 22 percent overall and 26 percent in attacks against large organizations.
The time from compromise to data exfiltration is longer only because espionage attackers require more time pivot between network resources, and find and exploit vulnerable systems before they’re able to move data to a command and control server. From the data, 84 percent of compromises are achieved within hours, and in 69 percent of breaches, data is moving off the network within hours.
Unfortunately for the victims, only 9 percent of breaches are discovered within hours. It’s taking months to years for most network intrusions to be discovered; 62 percent of breaches are found within months, 4 percent in years.
“Let’s stop treating [detection and response] like a backup plan if things go wrong,” the DBIR says, “and start making it a core part of the plan.”
Once discovered, most breaches are contained within days or weeks (76 percent), leaving a quarter to be contained within months or longer.
There is some tempered good news in that while 70 percent of breaches were discovered by third parties, down from 92 percent last year, detection capabilities seem to still be lacking within IT organizations. Another win is that external notification by organizations with no business relationship to the victim such as ISPs, and industry watchdog groups, climbed to 34 percent of breaches in cases of espionage. Fraud detection services and customer and law enforcement notification lead the way for financially motivated attacks.










