In the wake of the elimination of the federal cybersecurity czar position, the latest federal cybersecurity preparedness report from the Office of Management and Budget (OMB) and the Department of Homeland Security (DHS) shows that U.S. government is nowhere near ready for prime time when it comes to cyber-defense, with 74 percent of agencies lagging.
As mandated by President Donald Trump’s cybersecurity executive order issued last year, the risk report conducted a systemic audit of the security posture of federal departments and found that 71 of 96 of them are “at risk or high risk.”
These cyber risks can manifest themselves in many ways, including new attack vectors, the operation of outdated and unsupported IT and malicious links and email attachments. When it comes to all of these, agencies need to “take bold approaches to improve federal cybersecurity,” according to the report.
Further, the report said that across the board, agencies don’t have the information they need to determine how threat actors seek to gain access to their information, which in turn is leading to “ineffective allocations of agencies’ limited cyber-resources.”
The result? A damning picture emerges from the report, of enterprise-wide gaps in network visibility, a lack of IT tools and capability standardization, and no common operating procedures or policies. In fact, situational awareness is so limited that federal agencies could not identify the method of attack, or attack vector, in 11,802 of the 30,899 cyber-incidents (38 percent) that led to the compromise of information or system functionality in fiscal year 2016.
“One of the most significant security concerns that results from the current decentralized and fragmented IT landscape is ineffective identity, credential and access management processes,” OMB and DHS wrote. “Fundamentally, any organization must have a clear understanding of the people, assets, and data on its networks.”
Things are particularly bad when it comes to data loss and exfiltration prevention: only 40 percent of agencies report the ability to detect the encrypted exfiltration of information at government-wide target levels. Only 27 percent of agencies report that they have the ability to detect and investigate attempts to access large volumes of data.
Further, only 16 percent of agencies have properly implemented encryption on data at rest.
Joseph Carson, chief security scientist at Thycotic, told Threatpost that the stakes are high: “Information cyberwars have now become a major disruption to our way of life, filling our daily news and feeds with fake information to influence our actions and change the outcome of important and vital decisions, rather than focusing on important citizen needs like tax, health and education,” he said. “Many governments are now embroiled in trust and transparency challenges caused by the continuous disruption from cyberattacks. Many recent cyber-incidents have been stealing huge amounts of personal and sensitive information that is then being used to pursue and influence our decision-making.”
No Need for a Cybersecurity Coordinator?
The news comes hard on the heels of several senators calling on new national security advisor John Bolton to reinstate the position of cybersecurity coordinator on the National Security Council (NSC). Although the risk report details a lack of coordination and standardized tools and processes to be at the heart of the problem, the White House eliminated the coordinator position in mid-May, which was tasked with developing cyber-policy as a core function of national defense.
The New York Times reported at the time that according to an aide to Bolton, the central czar position established under the Obama administration was deemed unnecessary because lower-level officials had already made cybersecurity issues a “core function.”
“Today’s actions continue an effort to empower National Security Council Senior Directors. Streamlining management will improve efficiency, reduce bureaucracy and increase accountability,” NSC spokesman Robert Palladino said in a media statement at the time.
The move drew immediate backlash.
“I don’t see how getting rid of the top cyber-official in the White House does anything to make our country safer from cyber-threats,” Sen. Mark Warner (D-Va.), the ranking Democrat on the Senate Intelligence Committee, wrote on Twitter last week.
“This is a major mistake and a poor message to send to the world. Only a few months ago during the World Economic Forum (WEF), its latest report moved cyber-attacks to be the third greatest impact to global economies just behind natural disasters and climate change,” Carson told us. “This could be the second greatest mistake by the White House following the withdrawal of the Paris Agreement.”
A group of 19 Democratic senators sent a letter to Bolton last week urging him to reconsider the move, calling it a “step in the wrong direction.” It followed another bipartisan letter to the same effect, from Sens. Susan Collins (R-Maine) and Martin Heinrich (D-N.M.) to President Trump.
“Cyberattacks to our nation have increased in frequency and sophistication,” the senators, led by Amy Klobuchar (D-Minn.), wrote in the letter to Bolton. “Our country’s cybersecurity should be a top priority; therefore, it is critically important that the U.S. government present a unified front in defending against cyberattacks.”
That said, not everyone is concerned.
“Regarding the elimination of the White House position, frankly I’m not very worried,” Teresa Wingfield, director of product marketing at Nyotron, told Threatpost. “The real cybersecurity powers are with the NSA and that’s in the good hands of Rob Joyce.”
Joyce stepped down as cybersecurity coordinator shortly before the position was eliminated, to take up his NSA post.
OMB and DHS Recommendations
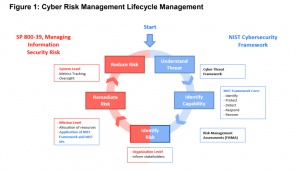
To help tackle the problem, OMB and DHS set out a few core actions that agencies should take, starting with information-sharing and a coordinated implementation of the NIST cyber-threat framework using a recommended Cyber Threat Framework, to prioritize efforts and manage cybersecurity risk. NIST’s framework for Improving Critical Infrastructure Cybersecurity creates standards for cybersecurity practices across various government agencies. This was a core tenet of Trump’s original cybersecurity executive order, handed down last May.
It cannot, however, exist in a vacuum as the only deterrent.
“Certainly, threat information plays a vital role in cybersecurity, but it’s no silver bullet,” said Wingfield. “According to Ponemon Institute, it takes a company an average of 206 days to detect a data breach, leading many to place a greater emphasis on threat intelligence. Most organizations lack the security staff to perform labor-intensive threat hunting. And, obviously, the damage is already done once the threat has penetrated security controls.”
Thus, the departments also recommend that agencies standardize their IT and cybersecurity capabilities to control costs and improve asset management – which is also a goal originally set out in Trump’s cybersecurity order. It explicitly said that the entire apparatus of the federal government must move to a shared, consolidated network architecture and IT infrastructure, including email and cloud services.
There is much work to do here: the report said that email, by way of phishing attacks, remains one of the most common attack vectors, thanks in no large part to sheer volume; the 23 civilian CFO Act agencies alone combine to have nearly 2.2 million email inboxes, with hundreds of thousands of additional inboxes across 100+ small agencies, OMB and DHS said.
“Standardizing and consolidating email at the enterprise level is a key element of the strategy for securing users, and yet some agencies report several separately managed email services inside their organizations,” the report said. “For example, one agency lists no fewer than 62 separately managed email services in its environment, making it virtually impossible to track and inspect inbound and outbound communications across the agency.”
Hand-in-hand with that initiative is the need to consolidate agency security operations centers (SOCs) to improve incident detection and response capabilities. This includes efforts at attribution.
“We hear about cyber-criminal groups that are behind many of the major cyber-incidents in recent years, whether it was a major data breach, ransomware or government agencies’ classified data being targeted,” said Carson. “Several companies and governments have linked these cybercriminal groups to nation-states though, without revealing concrete evidence and those nation-states denying any involvement. Without clear cooperation and transparency, this will continue to grow as a major problem, with a possibility of a full cyber-war as retaliation, and with no expert in the White House to see through the fog of threats then this could result in a major disaster.”
And finally, OMB and DHS recommend driving accountability across agencies through improved governance processes, recurring risk assessments and OMB’s engagements with agency leadership.