Researchers have identified eight malicious Android apps in the official Google Play marketplace distributing a new malware family. The “Haken” malware exfiltrates sensitive data from victims and covertly signs them up for expensive premium subscription services.
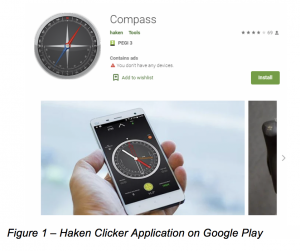
The eight apps in question, which have since been removed, had collectively been downloaded 50,000 times. The apps were mostly camera utilities and children’s games, including “Kids Coloring,” “Compass,” “qrcode,” “Fruits coloring book,” “soccer coloring book,” “fruit jump tower,” “ball number shooter” and “Inongdan.” The apps legitimately function as advertised, but in the background covertly perform an array of malicious functions.
“Haken has shown clicking capabilities while staying under the radar of Google Play,” said researchers with Check Point Research, in an analysis on Friday. “Even with a relatively low download count of 50,000+, this campaign has shown the ability that malicious actors have to generate revenue from fraudulent advertising campaigns.”
The downloaded Haken malware is what researchers call “clicker” malware, meaning that it mimics the user and clicks on anything that appears on the device’s screen. The impact of this on victims is two-fold. First, downloaded apps are able to sign users up for premium subscription services without them knowing. Second, this malware can access any sensitive information visible on the mobile screen – from work emails to work conversations over messaging apps.
After download, Haken communicates with a remote server and asks for permissions that the actual downloaded app doesn’t require in order to function (for instance, permission to let the app run code when a device starts up).
It then injects code into advertising monetization platforms for Facebook (Facebook Ad Center) and for Google (specifically Google AdMob), which would give the attackers access to the credit cards tied to these accounts. These accounts are used to pay for the premium subscription services, said researchers.
After reporting the threat to Google, all of the affected applications were removed from Google Play, researchers said.
When downloading apps, researchers warn that users should always be wary and check the apps’ reviews. For instance, the comments under the Google Play download pages for these specific eight apps described the apps acting suspiciously, serving as red flags for potential downloaders (See image below).

Click to enlarge.
The news comes a day after Google banned 600 apps for displaying disruptive advertising behavior that the company labels as mobile ad fraud.
“Mobile ad fraud is an industry-wide challenge that can appear in many different forms with a variety of methods, and it has the potential to harm users, advertisers and publishers,” said Per Bjorke, senior product manager for Ad Traffic Quality at Google, on Thursday. “At Google, we have dedicated teams focused on detecting and stopping malicious developers that attempt to defraud the mobile ecosystem. As part of these efforts we take action against those who create seemingly innocuous apps, but which actually violate our ads policies.”
Malicious apps continue to plague Google’s Play store. For instance, researchers recently pointed to fleeceware apps — which trick users into paying excessive amounts of money for simple apps with functionality that’s available free elsewhere – as ramping up in the marketplace.
Also, the Joker malware has proved to be a dangerous threat on Google Play: Google in January said it has removed 17,000 Android apps to date that were distributing the malware. Check Point researchers said on Friday that they have discovered four additional samples of the Joker malware on Google Play, which have been downloaded 130,000 times.