Researchers with F-Secure have tracked the top spam-related attachments and campaigns used so far in 2019. The verdict, ZIPs, PDF, and MS office files (such as DOC and XLSM file attachments) were more commonly used in huge spam campaigns than any other type attachment.
In addition, researchers noticed that disc image files (ISO or IMG files that store the content and structure of an entire disk, like a DVD or Blue-Ray) are increasingly being used to spread malware. This has been seen in a growing number of smaller campaigns distributing the AgentTesla malware and NanoCore remote access trojan, according to researchers.
“In February and March, we saw huge spam campaigns using ZIP files to send out GandCrab ransomware, and DOC and XLSM files to distribute Trickbot banking trojan,” researchers with F-Secure said in a post last week. “In the same time period, we saw a similarly large campaign targeting American Express [customers], and a ‘Winner’ scam, both using PDF file attachments.”
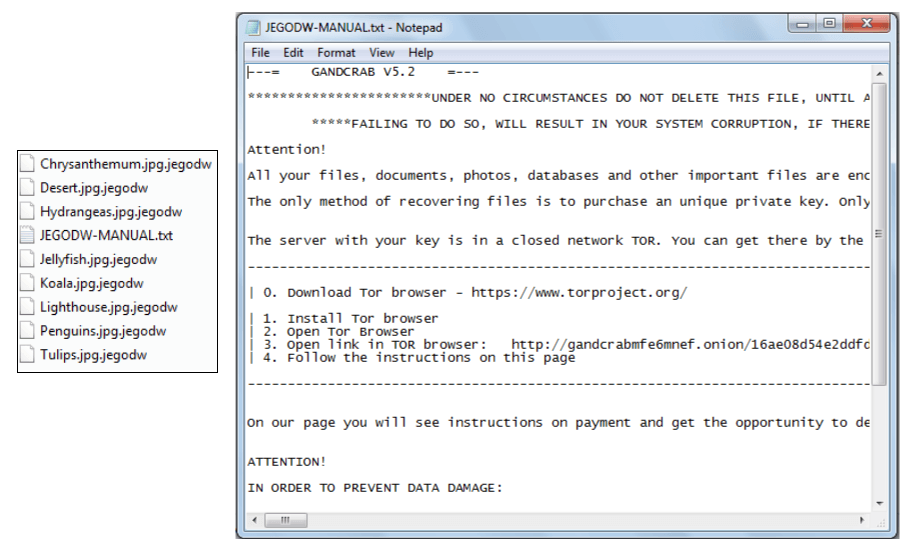
ZIP Files Spreading GandCrab
Researchers said that in February and March, there were huge spam campaigns spreading the infamous GandCrab ransomware. These campaigns were using ZIP files, designed to appear to be sending a photo to someone.
However, in reality the ZIP file contains a obfuscated JavaScript downloader, which executes a PowerShell script that downloads and executes the GandCrab ransomware binary. If the payload is successfully downloaded and executed, it then encrypts the victim’s machine and displays a ransomware note (below).
DOC/XLSM Files Delivering Trickbot
Researchers also noted huge spikes in tax-themed spam campaigns in March that were utilizing DOC and XLSM (macro-enabled spreadsheet created by Microsoft Excel) files to deliver the Trickbot modular banking trojan. The email sin the campaign, which were purporting to feature tax billing records, contained office doc attachments with a malicious macro that downloads and executed the payload using a bitsadmin tool. BitsAdmin is a legitimate command-line tool that can be used to create download or upload jobs and monitor their progress.
Once downloaded and executed, the Trickbot sample starts execution and creates modules on the victim’s machine, researchers said, stealing “as much data possible” – including banking credentials and more.
The TrickBot financial malware was first identified in 2016. Several recent campaigns demonstrate its fast paced evolution by those behind its development. Researchers have noted the malware’s new code-injection techniques, updated info-stealing module and a customized redirection method.
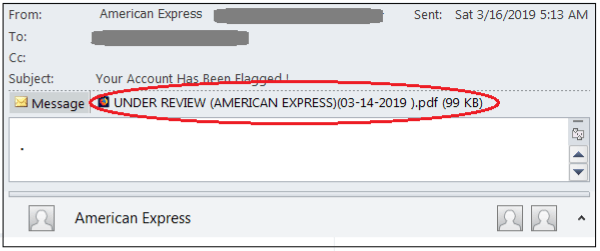
PDF Files Used in Amex Phishing
Another popular spam campaign in March revolved around a phishing attack that was making use of PDF files to target American Express customers.
“One of the highest spikes in the graph that used PDF is a phishing campaign targeting American Express during March,” researchers said.
The email purports to be from American Express, saying victims’ accounts have been flagged and featuring a PDF file that’s titled “Under Review.” When that PDF file is opened, it shows a link that leads the user to a “secure message” pretending to be from the American Express Business Card Customer Security Team. In reality the link leads the victim to a malicious landing page with a shortened URL – to further deceive victims that it’s fake – and asks for their banking credentials.
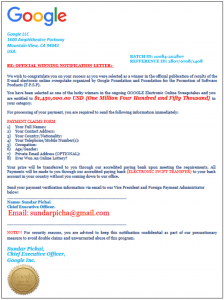
PDF Files Used For ‘Winner Scam’
Researchers also observed a “Winner” scam, which they said was the second-highest campaign using a PDF file attachment spread via email.
The attachment, claiming to be sent from Google, tells victims they won an email online sweepstake of $1.4 million, organized by the Google Foundation and Foundation for the Promotion of Software Products.
The form then asks for personal details, and for victims to send their payment verification information via email to Google CEO Sunday Pichai at “sundarpicha@gmail.com.”
“The scam asks the victim to provide personal details such as full name, address, country/nationality, telephone/mobile number, occupation, age/gender, and private email address,” researchers said.
A message at the end of the email tell victims: “For security reasons, you are advised to keep this notification confidential as part of our precautionary measure to avoid double claims and unwarranted abuse of this program.”
ISO and IMG Delivering AgentTesla
Interestingly, researchers said that they’ve noticed a spike in attackers using disc image files (ISO and IMG files) to deliver malware since July 2018. The ISO image file is a snapshot of the data and layout of a CD; while the IMG disc image file created by various disc imaging applications.
Most notably, researchers have seen a growing number of campaigns – which albeit are smaller – using this technique to deliver AgentTesla information stealer malware and NanoCore RAT.
“Interestingly, we also have seen a recent spam campaign delivering two types of attachments: A malicious office doc and ISO image file – both installs an AgentTesla infostealer,” they said.
In these campaigns, a malcious doc would execute a macro to download and execute the payload; while the ISO file would contains a malicious binary inside it.
“Regardless of which of the two attachment types the victim chooses to open, either will install AgentTesla – an infostealer that is capable of collecting the victim’s system information and credentials from popular installed software such as browsers, email clients, and ftp clients,” said researchers.
Spam Campaigns Evolving
Spam campaigns continue to adopt new tactics that make them harder to spot – and the usage of new types of attachments, such as the ISO image file described above – only makes it easier for attackers to deceive their victims.
In fact, according to recent research, spam is the most common method for cybercriminals to spread malware overall in 2018, accounting for nine out of every 10 infection attempts throughout the year.
Roughly 69 percent of spam campaigns attempted to trick users into visiting malicious URLs to download a malware-laden file or committing another online action that results in an infection.
Malicious attachments were used in the remaining 31 percent of these campaigns.
“Malware authors tend to prefer specific types of file attachments in their campaigns to distribute malicious content,” F-Secure researchers stressed.